The Beyond Blog
17 Feb 2026
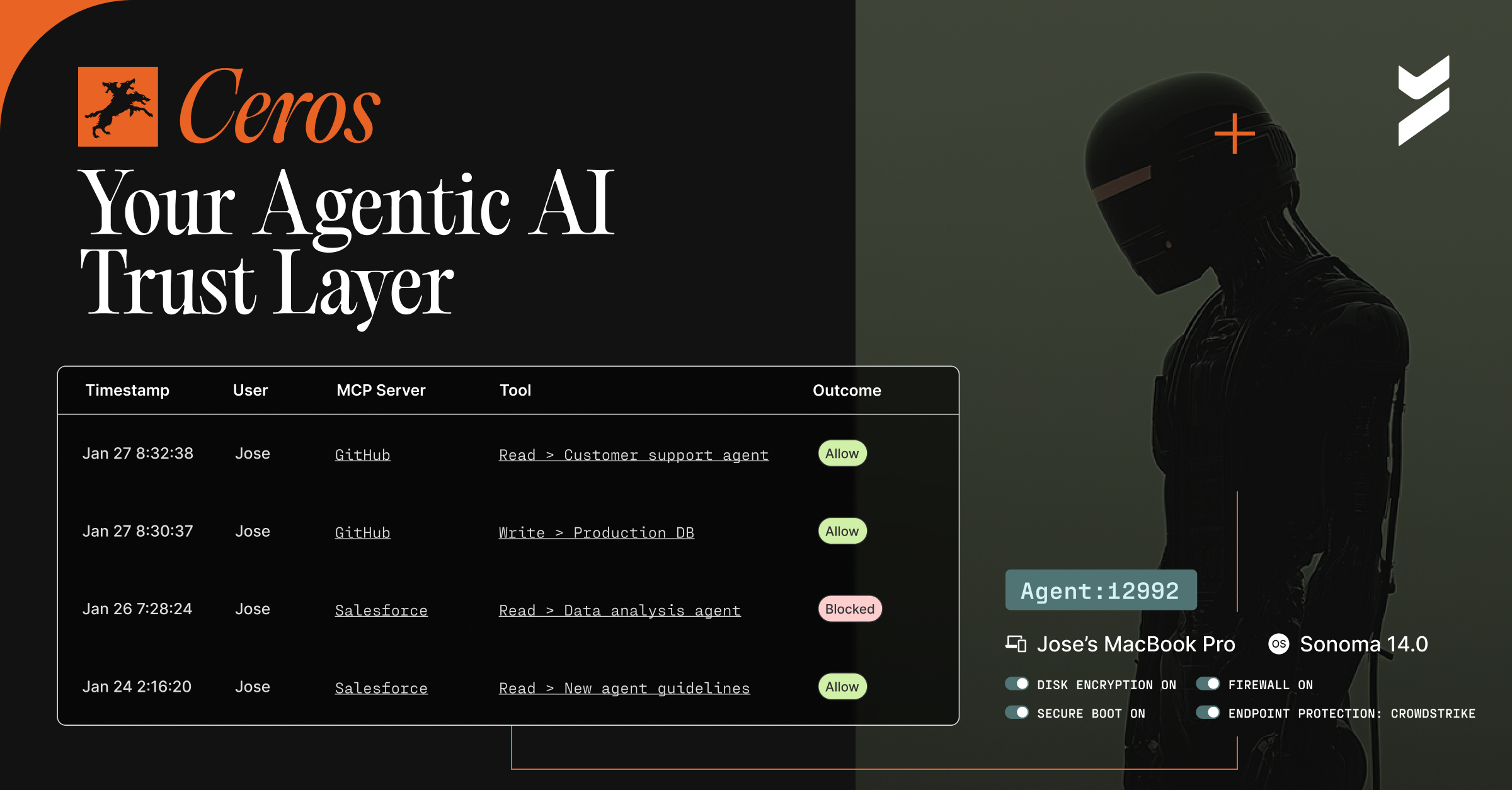
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.

25 May 2022
May 25, 2022
What to Know From the 2022 Verizon Data Breach Investigations Report (DBIR)
The 2022 Verizon DBIR is full of insights and data about the current state of cybersecurity. Here are the top five takeaways you need to know.

17 May 2022
May 17, 2022
Why the GitHub 2023 2FA Mandate isn't Enough
This 2FA initiative from GitHub is designed to improve the overall security of the software supply chain, but it doesn’t go far enough.

11 May 2022
May 11, 2022
NIST and Passwordless Solutions: Meeting Compliance Needs
The truth is that passwordless authentication is NIST 800-63 compliant and a much better solution than simply improving your password policies.

04 May 2022
May 4, 2022
Why Your MFA Is Insecure
Using multiple insecure authentication mechanisms provides little security and many MFA solutions today still leave companies vulnerable to attack.

29 Apr 2022
April 29, 2022
Countries With the Most—and Least—Digital Freedom
Beyond Identity compiled data from Freedom House’s 2021 Freedom on the Net report to rank the countries with the most and least digital freedom.

27 Apr 2022
April 27, 2022
5 Things a Modern MFA Should Do
There are five essential features that any secure, modern MFA should have to truly protect users and a company’s sensitive data and systems.
![Measuring Password Fatigue: Usability and Cybersecurity Impacts [Study]](https://cdn.prod.website-files.com/6835da5ccf38540935c3c9c1/6890d5e2603e93d7e44b57cc_65e76633020fbc21c382d09b_hd_800x415.avif)
25 Apr 2022
April 25, 2022
Measuring Password Fatigue: Usability and Cybersecurity Impacts [Study]
Passwords are meant to be a convenient security measure. However, password fatigue might be affecting your cybersecurity and mental health without you even knowing.

14 Apr 2022
April 14, 2022
Strengthening Industry Authentication Standards with the TPM
Learn how Beyond Identity connects and uses existing standards to improve the convenience and security of user authentication.

13 Apr 2022
April 13, 2022
Passwordless, Unphishable MFA for Practically Any SSO in the Market!
We’re excited to share we’ve expanded support to customers who are using an SSO from CyberArk, Google, OneLogin, Shibboleth, and VMware.

