The Beyond Blog
17 Feb 2026
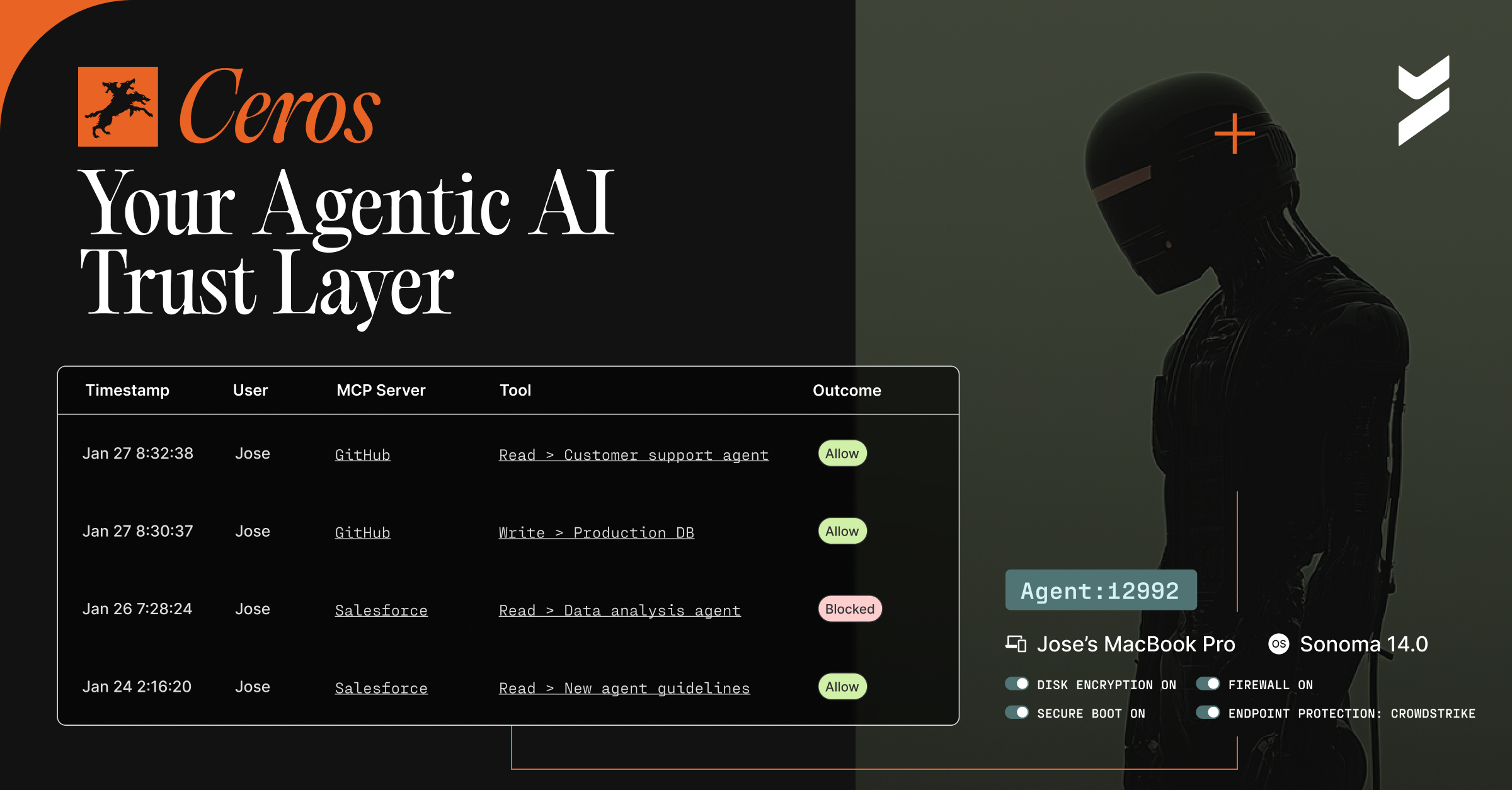
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
.avif)
06 Mar 2023
March 6, 2023
Beyond Identity + NextAuth.js
If you are implementing authentication in Javascript, then chances are you’ve heard of NextAuth.js (becoming Auth.js). Auth.js is a complete open-source authentication solution for web applications.

03 Mar 2023
March 3, 2023
Passkeys: Building Blocks for Passwordless Authentication
So how do you protect your network and its users from this rising threat? The answer is surprisingly simple: passwordless authentication using passkeys.
21 Feb 2023
February 21, 2023
Hacker Tracker: February 2023
The new year has kicked off with cybercriminals picking up where they left off in 2022. In January we saw a string of attacks against major companies, government agencies, and NGOs

16 Feb 2023
February 16, 2023
Binding Identity to Device
Businesses are becoming increasingly digital and secure authentication is now a necessity, not an option.

15 Feb 2023
February 15, 2023
Everything You Need to Know About the Bridge to Zero Trust Virtual Event!
For the last decade, adversaries have been stealing credentials and logging into systems as legitimate users. More recently attackers have honed their tactics, and they are now bypassing first generation MFA designed to fix this issue at an alarming rate.
20 Jan 2023
January 20, 2023
What are Passkeys?
As a developer, you've probably heard of passkeys. But what are they exactly? And why should you care?

20 Jan 2023
January 20, 2023
Cybersecurity Risks of Improper Offboarding After Layoffs
Offboarding an employee can be a cybersecurity risk, so we studied the specifics of improper offboarding and its consequences.
18 Jan 2023
January 18, 2023
Hacker Tracker: January 2023
Read on for Beyond Identity's analysis of high-profile cyberattacks, and more, that took place during January 2023.

17 Jan 2023
January 17, 2023
Credential Theft and Signing Fools
What makes Beyond Identity, or any other company, phishing-resistant. It’s a great question and our CTO Jasson Casey has the answer.

