The Beyond Blog
17 Feb 2026
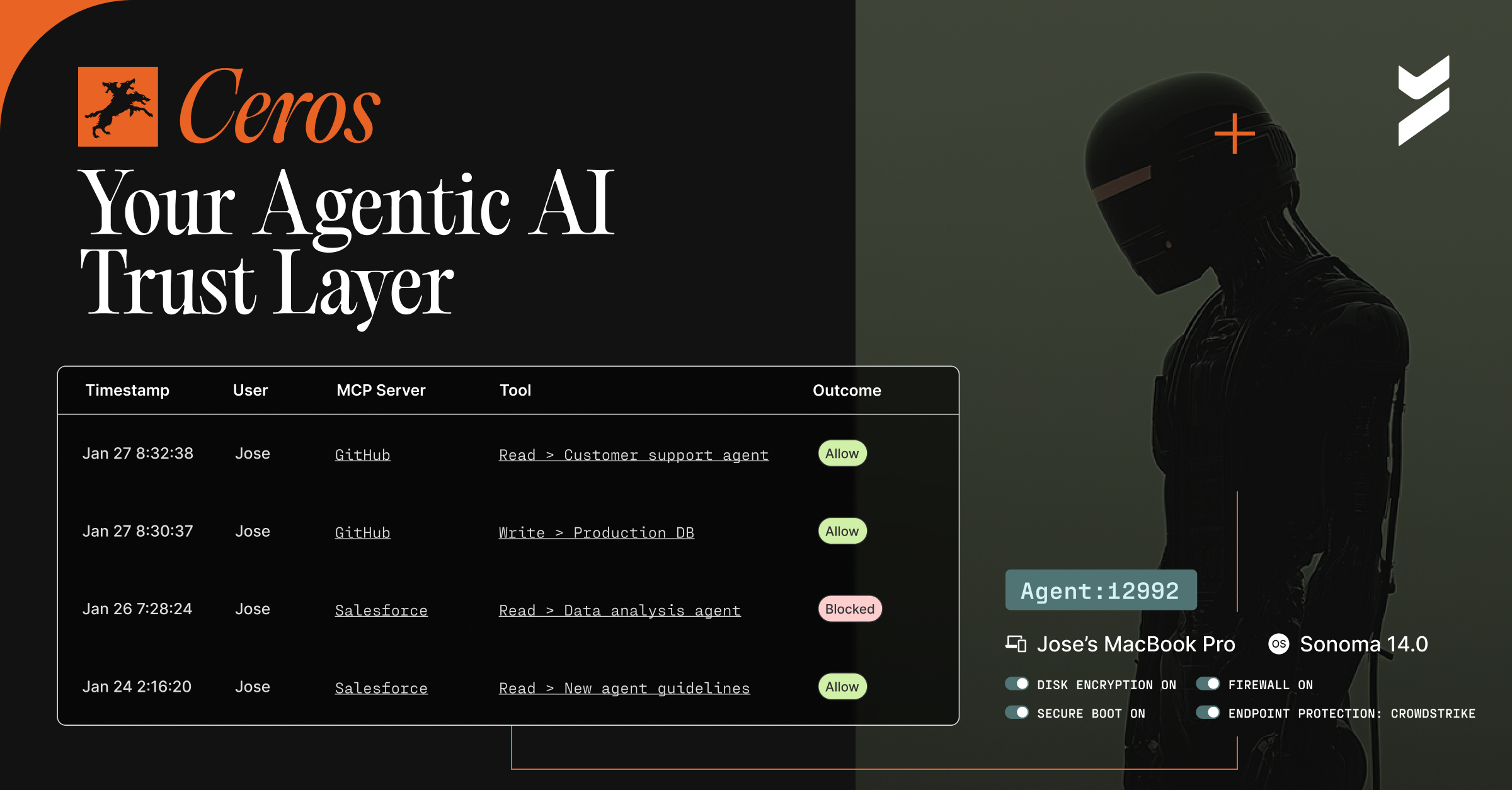
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
18 Apr 2023
April 18, 2023
Hacker Tracker: April 2023
Welcome to Hacker Tracker, where we report on and analyze the past month’s most significant cyberattacks. Spoiler alert: it’s never good.
17 Apr 2023
April 17, 2023
Q1 2023 New Features Announcement
As a developer, your job is to build awesome products, not authentication. That's why we're excited to announce new features in Beyond Identity's Secure Customers product that will help you offload the work of authentication.

14 Apr 2023
April 14, 2023
How to Choose an Authentication Method for Your New Project
Building a new app or website can be a daunting task, and one of the most important decisions you'll make is choosing an authentication method.

31 Mar 2023
March 31, 2023
What You Missed at The Bridge to Zero Trust Virtual Event
Top cybersecurity experts discuss the combination of identity, authentication, network architecture, and endpoint detection and response technologies.

24 Mar 2023
March 24, 2023
Five Takeaways from the Zero Trust Leadership Series Kickoff
Here are five key takeaways from our March 15, The Bridge to Zero Trust event. Register now to watch the replays.
21 Mar 2023
March 21, 2023
Hacker Tracker: March 2023
Read on for our breakdown of the most high-profile hacking news—ransomware or otherwise—from February.

20 Mar 2023
March 20, 2023
Beyond Identity's Zero Trust Authentication Under the Hood
There are seven key tenets of Zero Trust Authentication. All of them are critical, so we’ll review them one-by-one and show you what it looks like.

15 Mar 2023
March 15, 2023
About The Bridge to Zero Trust Virtual Event
We’ve invited top industry leaders and specialists to join us for a discussion about the future of cybersecurity and the role of zero trust architectures.

14 Mar 2023
March 14, 2023
Dr. Zero Trust on Zero Trust Authentication
Chase Cunningham, Dr. Zero Trust, discusses Zero Trust Authentication, a new book you should read, and a must-attend virtual event.

