The Beyond Blog
17 Feb 2026
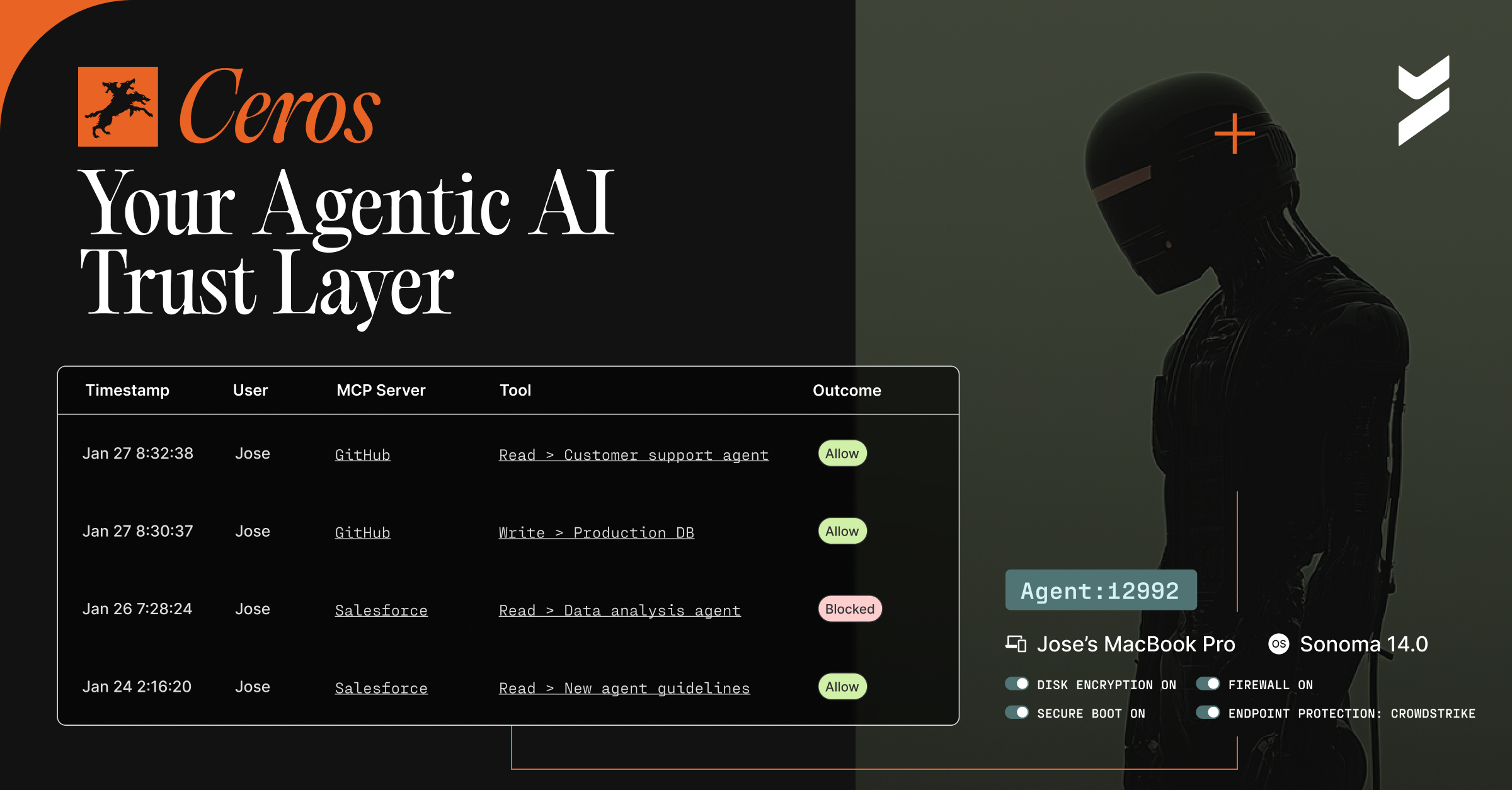
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.

29 Nov 2021
November 29, 2021
Frictionless Authentication Across eCommerce, Media, Travel, and Fintech Industries
Frictionless authentication done right addresses common pain points and eliminates the possibility of compromised accounts due to weak or stolen passwords.

18 Nov 2021
November 18, 2021
PSD2 Compliance Requirements: How to Meet Them with Passwordless Authentication
The PSD2 is an attempt by the EU European Banking Authority to address consumer protection and how third-party providers access banking data. Here's what you need to know.
18 Nov 2021
November 18, 2021
3 CI/CD Pipeline Security Best Practices
Many companies are failing to secure their DevOps pipelines, leading to high profile cyberattacks like the SolarWinds hack. Here are three best practices for securing your CI/CD pipeline.

10 Nov 2021
November 10, 2021
5 Mobile Device Management Best Practices
The rapid transition to remote work presented an entirely new set of security risks and threats. Now is the time to review your mobile device management practices.

09 Nov 2021
November 9, 2021
What is Step-Up Authentication: How it Works and Examples
Step-up authentication provides an alternative that allows companies to tailor authentication processes based on risk in a way that is secure, scalable, and user-friendly.

05 Nov 2021
November 5, 2021
Thwart Supply Chain Attacks by Securing Development / Build Vulnerabilities Webinar Recap
Software supply chain attacks are on the rise and it's time to do something about it.

05 Nov 2021
November 5, 2021
The New Cybersecurity Perimeter: Part 1
What is the new cybersecurity perimeter and what brought about the change?

29 Oct 2021
October 29, 2021
3 Alternative Authentication Methods for Online Customers
Passwords aren’t working for the modern business, but there are other options. Switching to an alternative authentication method can improve e-commerce security and the user experience.

28 Oct 2021
October 28, 2021
Software Supply Chain Attack Methods Behind Solarwinds, Kaseya, and Notpetya and How to Prevent Them
Here are the stories of the most famous software supply chain attacks to date and how the cybercriminals behind them were able to pull them off.

