The Beyond Blog
17 Feb 2026
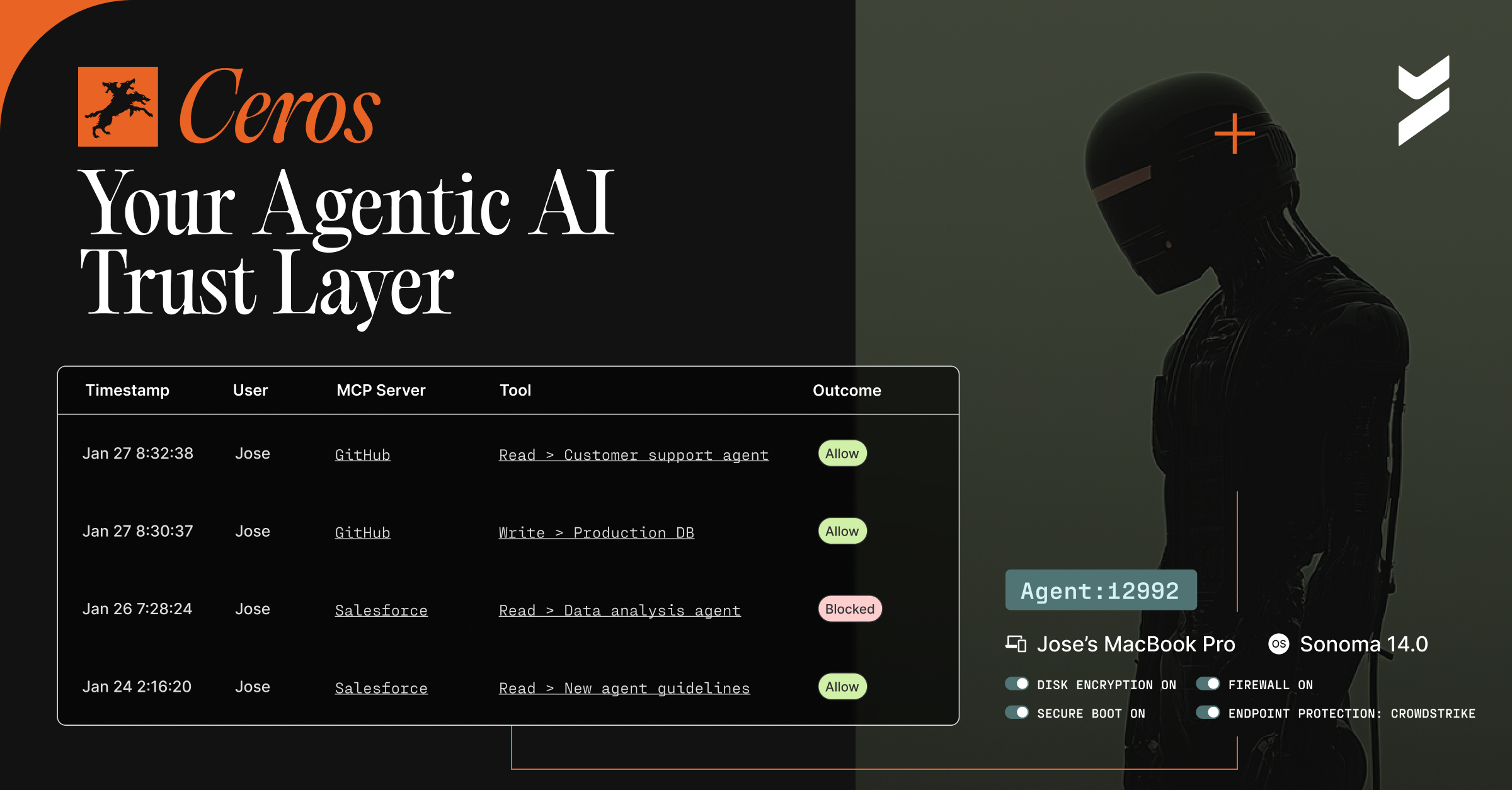
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
28 Oct 2021
October 28, 2021
5 Unsolved Cybersecurity Attacks
Some cybersecurity attacks remain a mystery forever. Here are five unsolved cyberattacks where the hacker was never discovered.
![Lost Value in Customer Authentication Frustration [Survey]](https://cdn.prod.website-files.com/6835da5ccf38540935c3c9c1/6890d5735062d22cb67f63f7_65e762c66408c38465c440bd_lost-value-in-customer-authentication-frustration.avif)
27 Oct 2021
October 27, 2021
Lost Value in Customer Authentication Frustration [Survey]
Based on the responses of over 1,000 consumers, it can be safely concluded that passwords are the number one hurdle for account creation and transactions.
![Would You Rather Be Hacked? [Survey]](https://cdn.prod.website-files.com/6835da5ccf38540935c3c9c1/6890d60b31130ae2aa315502_65e76235c8599da00c5ab3c9_would-you-rather-be-hacked_1.avif)
26 Oct 2021
October 26, 2021
Would You Rather Be Hacked? [Survey]
We surveyed full-time employees to examine what they would rather have hacked in terms of their work, social, and personal accounts.

26 Oct 2021
October 26, 2021
5 Types of Security Vulnerabilities in E-commerce and How to Protect Against Them
Leaving security vulnerabilities in e-commerce unaddressed can cause significant damage to a company and its customers, erode customer trust, harm the bottom line, and even potentially put an organization in legal jeopardy.

21 Oct 2021
October 21, 2021
Stop Bot-Executed Credential Attacks with Passwordless Authentication
Bots are a rising issue for customer-facing applications. Here’s how passwordless authentication can help you protect customers from bot attacks.
13 Oct 2021
October 13, 2021
Password-Palooza Webinar Recap
Let’s address some common myths and misconceptions about securing your software development lifecycle to stop software supply chain attacks
13 Oct 2021
October 13, 2021
10 Secure Software Development Myths
Let’s address some common myths and misconceptions about securing your software development lifecycle to stop software supply chain attacks
04 Oct 2021
October 4, 2021
Zero Trust vs VPN: Is it Time to Ditch VPNs?
We’ve used VPNs for decades, and they have become more commonplace. But there are performance and security concerns with VPNs that are becoming painfully apparent.
29 Sep 2021
September 29, 2021
Introducing Zero-Friction Passwordless Authentication for Customers that Eliminates Account Takeover Fraud
Beyond Identity launches omnichannel passwordless authentication for customers that accelerates conversions and completely eliminates account takeover fraud.

