The Beyond Blog
17 Feb 2026
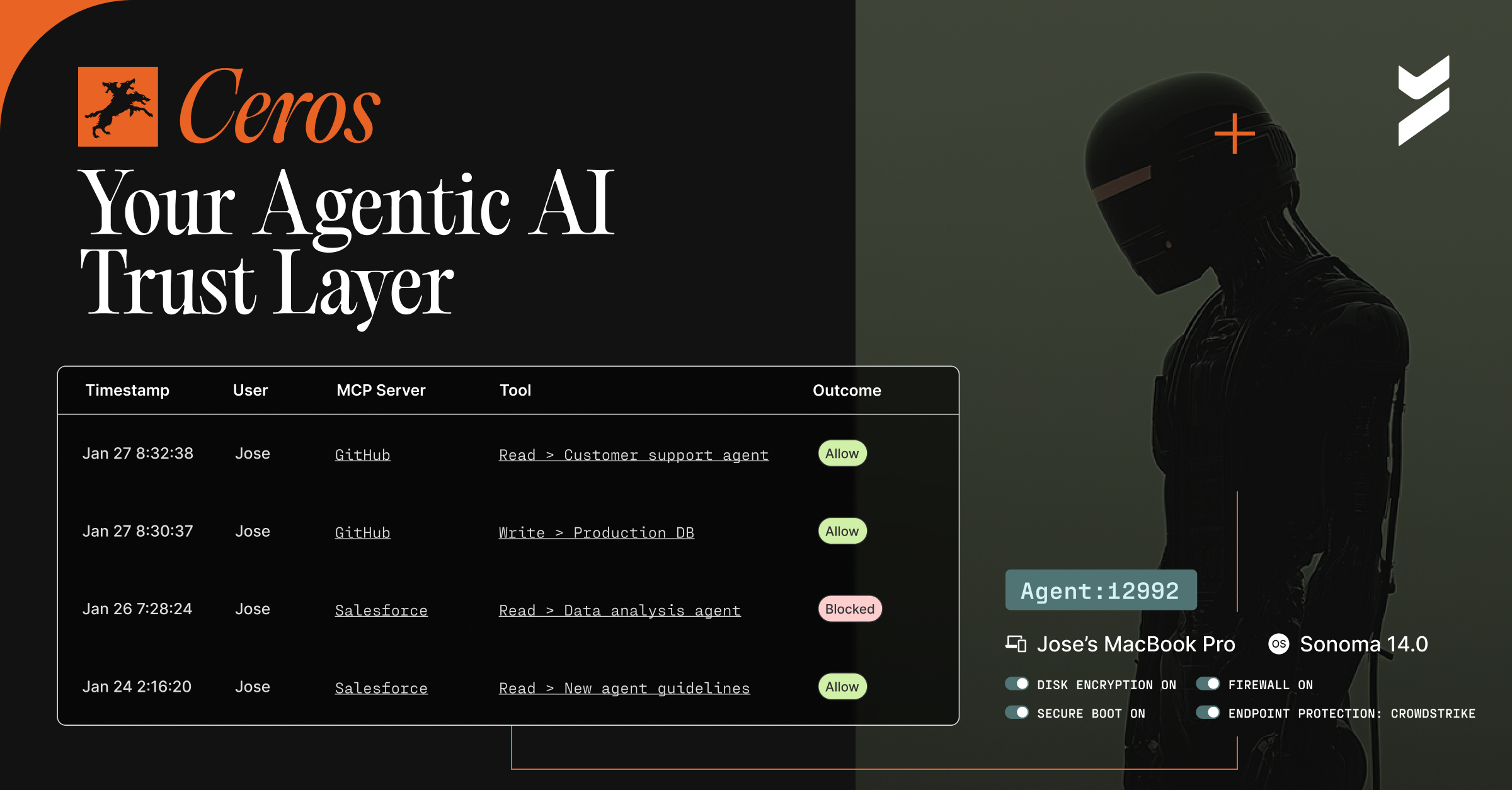
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.

03 Jan 2022
January 3, 2022
Level Up Microsoft Conditional Access with Beyond Identity’s Device Security Checks
Our integration with Azure AD SSO and other SSOs authenticates users with the strongest and most reliable factors and checks the security of every device.
03 Jan 2022
January 3, 2022
Code Injection Attack: What It Is and How to Prevent It
Code injections pose a significant threat to enterprise cybersecurity. Protecting against code injection attacks is essential for organizations.
30 Dec 2021
December 30, 2021
Secure SDLC Best Practices
Developers can secure the SDLC and reduce the number of vulnerabilities that reach production. Here are four best practices to follow to secure the SDLC.

22 Dec 2021
December 22, 2021
Passwordless MFA vs One-Time Codes
Not all MFA is created equal, but the ones widely used are not the best for customers. Learn the difference between one-time codes and passwordless MFA.
21 Dec 2021
December 21, 2021
Announcing MISA Partnership and Microsoft Azure AD SSO Integration
We’re excited to announce that we’ve joined the Microsoft Intelligent Security Association and we’ve launched an integration with Microsoft Azure AD SSO!
![Are Password Resets Costing Your Company? [Survey]](https://cdn.prod.website-files.com/6835da5ccf38540935c3c9c1/6890d53e77516719c3203e2b_65e763688afdacd1d193c0df_header_800x415.avif)
17 Dec 2021
December 17, 2021
Are Password Resets Costing Your Company? [Survey]
Are passwords keeping consumers from both online and offline experiences? The results of this study might surprise you.
![How to Stop Malicious Code Injection at Repo [Infographic]](https://cdn.prod.website-files.com/6835da5ccf38540935c3c9c1/6890d56a09b9b2726a6212be_65e7632ed68690ec7206cc5e_malicious-code.avif)
08 Dec 2021
December 8, 2021
How to Stop Malicious Code Injection at Repo [Infographic]
Between Solarwinds, NotPetya, and Kaseya, thousands of companies have been impacted by software supply chain attacks and have cost billions of dollars in damages.

30 Nov 2021
November 30, 2021
The Importance of User Experience in Customer Authentication
A clean customer authentication UX can help to bring your business to the next level of success, and it’s not as difficult as you might think.

30 Nov 2021
November 30, 2021
How to Protect Your Source Code
Companies face a number of different threats to the security of their source code. However, they can mitigate or eliminate these source code security risks by taking a few steps.

