The Beyond Blog
17 Feb 2026
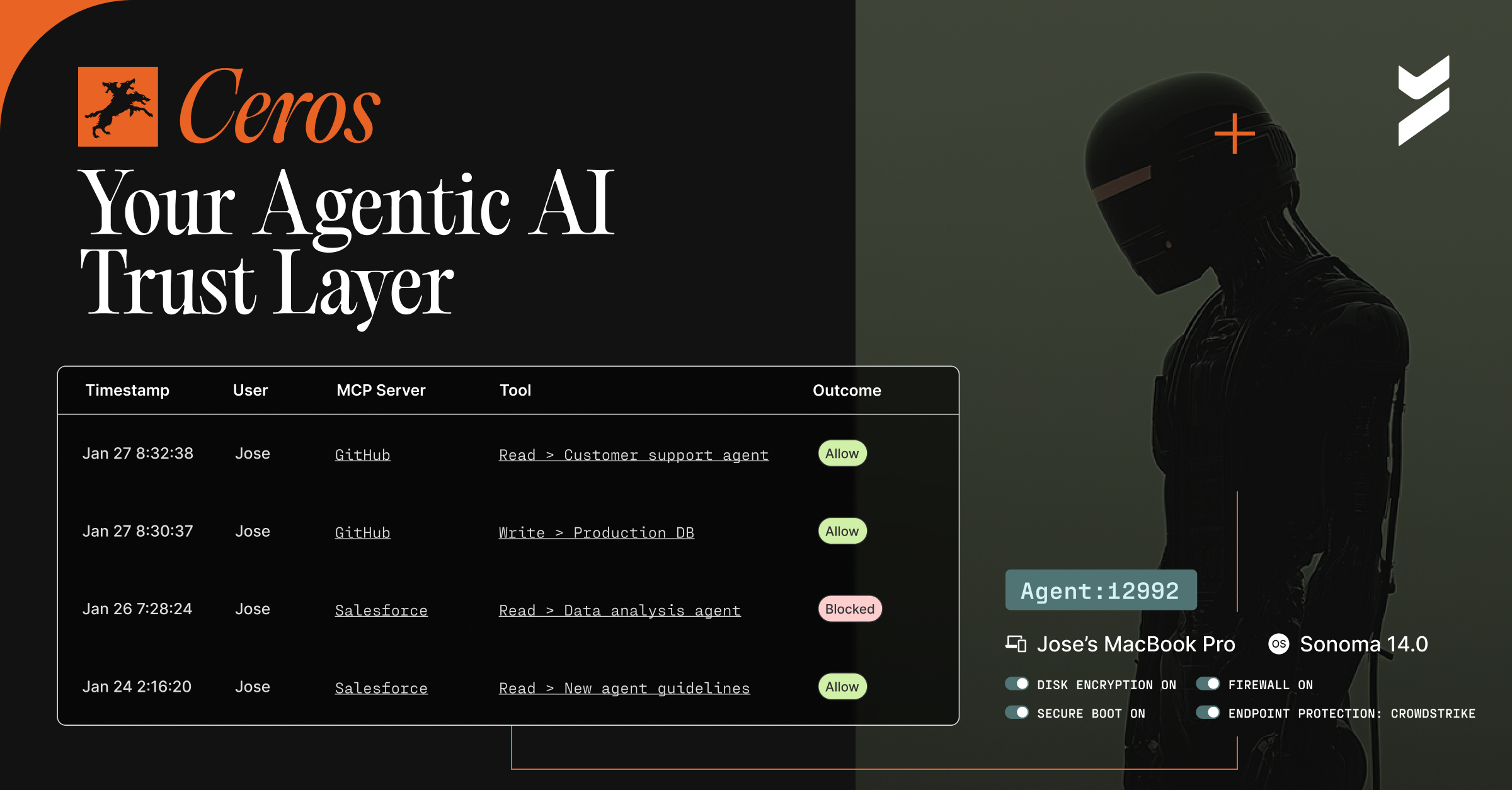
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.

26 Aug 2022
August 26, 2022
5 Risks to Your Current Code Signing System
Learn about five threats to the code signing system and how organizations can mitigate these risks by ensuring every commit is signed by verified corporate identities.

24 Aug 2022
August 24, 2022
Steps to Secure Your SDLC
The Secure SDLC integrates security into the SDLC. At each stage of the SSDLC, companies and developers can take steps to improve security.

22 Aug 2022
August 22, 2022
10 States Most at Risk for Malware Attacks
Using SonicWall data, Beyond Identity highlights the 10 states with the most attempted malware attacks.
04 Aug 2022
August 4, 2022
Better BYOD: Maintaining Security and Employee Privacy
Fighting against BYOD doesn’t work. Employees need the flexibility to use whatever device they need. At the same time, they need their privacy respected.

03 Aug 2022
August 3, 2022
5 GitHub Security Best Practices
Software supply chain exploits have become a growing threat in recent years . Here are five best practices for securing your organization’s code on GitHub.

22 Jul 2022
July 22, 2022
A Digital Dive Into Brand Security (Survey)
Cybersecurity for personal devices is important. Find out which brands are doing the most for protecting your privacy from a survey of consumers.

21 Jul 2022
July 21, 2022
How Do Chrome Users React to Password Alerts? (Survey)
Google Chrome’s security alerts expose password weakness and reveal a need for better authentication standards.
19 Jul 2022
July 19, 2022
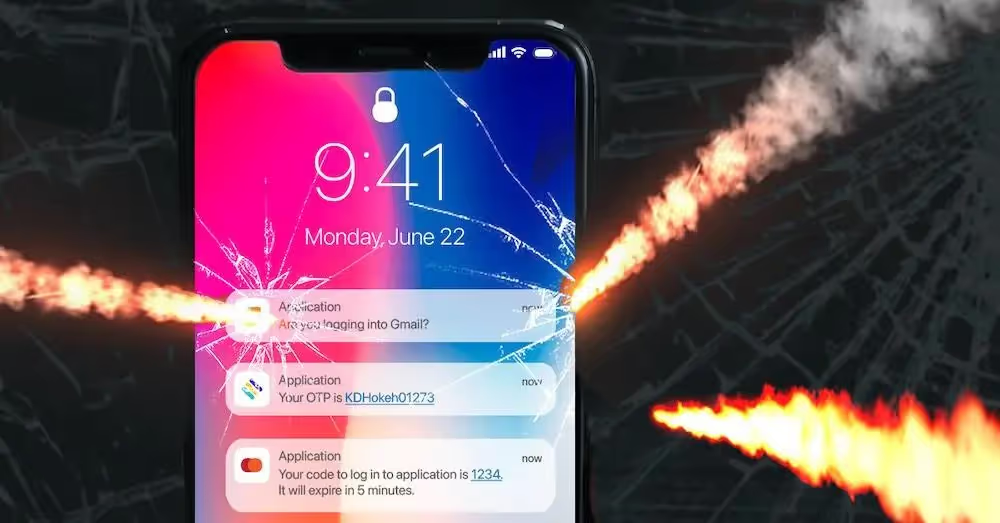
Password-Based MFA Vulnerabilities
Learn about the most common MFA vulnerabilities and steps you can take right now to protect your organization from an increasing number of cyberattacks.
19 Jul 2022
July 19, 2022
Introducing Self-Serve Access to Secure Customers SDKs and APIs
With access to our SDKs and APIs, developers can embed invisible, passwordless MFA that eliminates account takeover fraud and works across all platforms.

