The Beyond Blog
17 Feb 2026
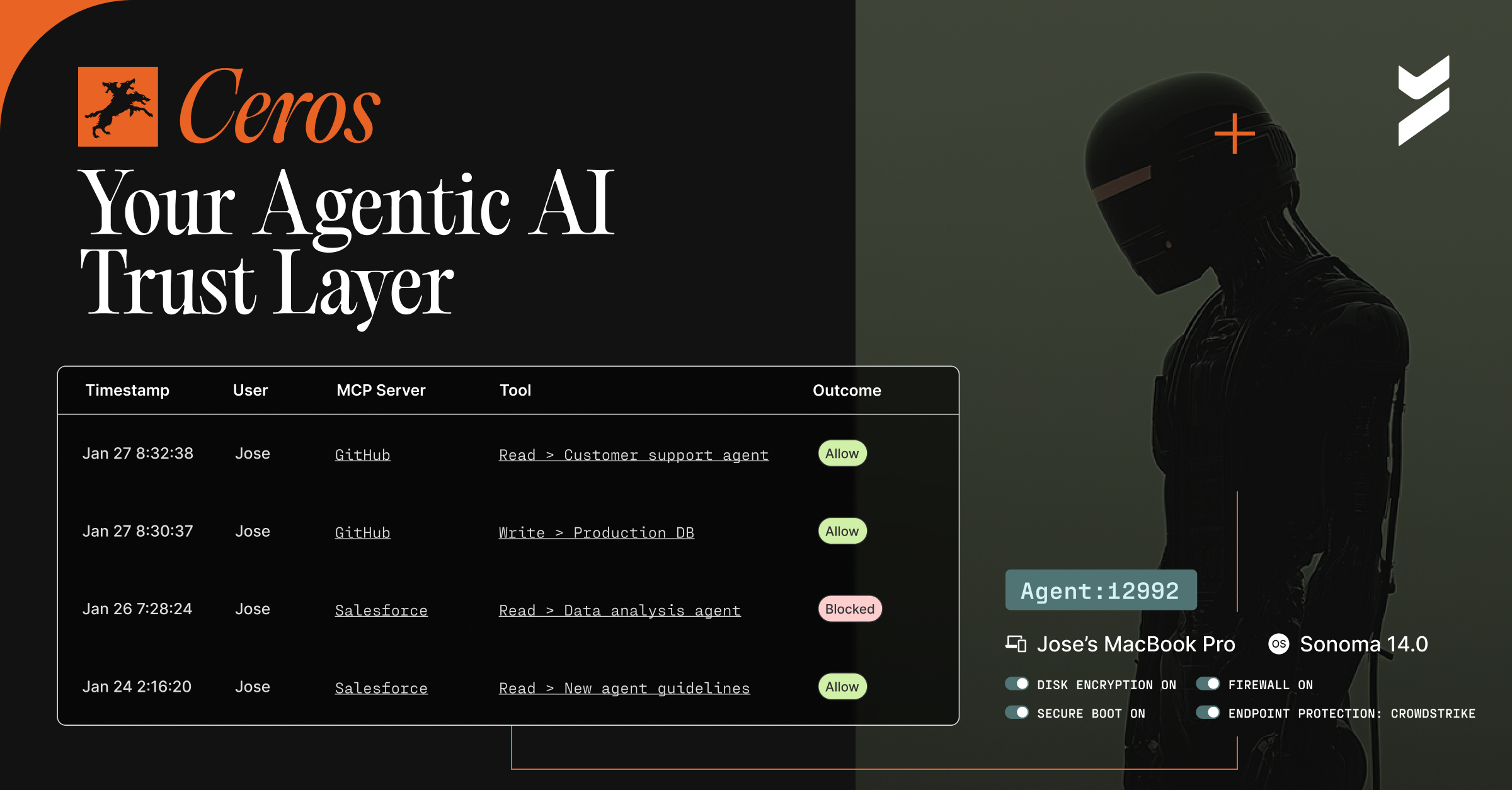
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
.avif)
28 Oct 2025
October 28, 2025
NYDFS Part 500 in 2025: Key Deadlines, New Requirements, and Compliance Strategies
Navigate NYDFS Part 500's November 2025 deadlines with confidence. Explore governance changes, personal liability rules, enforcement actions, and how to prepare.

17 Oct 2025
October 17, 2025
From Reactive to Proactive: A Practitioner's Guide to Zero Trust After the F5 Breach
The F5 breach highlights the need for a proactive security model. Learn how to implement dynamic identity defense against sophisticated threats to achieve Zero Trust.
.avif)
09 Oct 2025
October 9, 2025
FIDO Is Not Enough for Enterprise Security
If your organization is evaluating passkey deployments, it is irresponsible and insecure to deploy synced passkeys with FIDO. Learn more.
.avif)
02 Oct 2025
October 2, 2025
CVE-2025-59363: OneLogin Breach Highlights Urgent Need to Secure Non-Human Identities
A critical OneLogin vulnerability (CVE-2025-59363) exposes OIDC secrets, highlighting the risks of shared credentials for human and non-human identities. Learn more.
.avif)
01 Oct 2025
October 1, 2025
The Unpatchable User: The Case for Continuous Device Security
Your employee's outdated phone is full of vulnerabilities but she still needs to work. Discover how dynamic access control balances security with productivity in hybrid workplaces.
.avif)
25 Sep 2025
September 25, 2025
Goodbye Legacy Microsoft MFA: Future-Proofing with Modern Authentication
Microsoft will be deprecating legacy FA and self-service password reset policies September 30, 2025. Here's what you need to know to prepare your business for the transition.

23 Sep 2025
September 23, 2025
Machine Credentials Are Identities, It's Time to Treat Them That Way
Non-human identities outnumber humans 50:1. Learn why strong credentials are critical to securing bots, APIs, and service accounts.
.avif)
15 Sep 2025
September 15, 2025
Universal Identity Defense for Legacy and On-Prem Applications with Beyond Identity and CrowdStrike
Extend phishing-resistant MFA to Kerberos, NTLM, LDAP, SMB with Beyond Identity + CrowdStrike.
.avif)
03 Sep 2025
September 3, 2025
The Unseen Threat: Why Non-Human Identity (NHI) is the Next Frontier in Security
Non-human identities (NHIs) — devices, workloads, APIs, and AI agents — are now the fastest-growing attack surface. Learn why compromised NHIs fuel breaches, why traditional IAM fails, and how Beyond Identity secures every identity with phishing-resistant, passwordless authentication.

