Beyond Identity is Conquering Cross-Platform Woes for Passwordless Authentication
Passwordless authentication solutions aim to effectively shrink the available attack surface of organizations by removing passwords from the authentication workflow. However, not all passwordless solutions have the same capabilities or features; some of these missing capabilities have created barriers, stagnating passwordless adoption.
In general, widespread adoption of passwordless authentication is hindered by concerns related to usability and cross-platform functionality, with the biggest being the ability to use a particular passwordless authentication method on all device operating systems interacting with organizational resources, most specifically, the ability to remove password prompts in every authentication workflow.
Organizations focused on securing workforce access to critical resources will find this blog post most valuable as we will review these chief concerns surrounding passwordless authentication adoption and cross-platform operability.
Most Passwordless Solutions Were Not Developed To Operate Across Device Platforms
Passwordless authentication, in practice, removes passwords as an authentication factor, though not all “passwordless” authentication eradicates passwords from the authentication workflow as Beyond Identity does. Most “passwordless”, while much more secure than using a password, poses several barriers to adoption. One of those is cross-platform functionality. For example, with Windows Hello For Business, there are no uniform, simple, and seamless solutions to support passwordless access from non-Microsoft devices. People who use an Apple tablet for architectural designs, an Android phone to access Salesforce, or a laptop running a Linux OS for development would still need to use passwords to authenticate and gain access to resources.
The problem many passwordless providers sought to solve was the user experience. If passwordless providers cannot solve passwordless authentication for all use cases, then they’re left with keeping the password as a backup or alternative authentication method for some situations or devices. Passwordless solutions that do not completely eliminate the password from the authentication flow, in all situations, were not built with security requirements of a modern workforce in mind, unlike Beyond Identity.
Why Does Cross-Platform Support Matter for Passwordless?
The requirements of a modern workforce not only demand an answer for cross-platform operability for passwordless authentication, but they also require it to improve the security posture of the organization. These cross-platform challenges force security and identity professionals to reconsider what should be defined as a secure solution for passwordless based on the use cases and needs of businesses transitioning to, or firmly invested in, SaaS applications and cloud computing.
Because Removing Passwords is the Point of Passwordless Authentication
Password-based attacks are the vector of choice for cybercriminals targeting corporate organizations, with over 80% of hacking-related incidents involving credentials and passwords. To appropriately protect against the most significant contributor to data exfiltration, and to eliminate passwords entirely as a threat vector, all users must have secure access to resources, regardless of the device type or operating system they use to request access.
Failing to remove passwords for users on all devices fails to meet the base requirement of passwordless authentication—removing passwords as a factor for authentication.
Because Every Device Is A Work Device
The expansion of work from home and rapid adoption of cloud services has erased the traditional network perimeter, replacing it with sometimes thousands of user endpoints, some managed and others personal devices leveraged for work. In addition, cybercriminals target remote workers, credential stuffing attacks are rising, and 47% of surveyed remote professionals are falling for phishing scams that fuel even more password-based attacks. Therefore, strong passwordless authentication must operate on and ensure the security state of managed and unmanaged devices across platforms and device types to adapt to and defend against evolving cyber risks.
Today, every endpoint is an opportunity for data compromise, so personal devices must be made as secure as company-issued laptops to protect critical resources.
Because Improved Usability Improves Adoption and Compliance
Cross-platform support would ensure consistent experiences for passwordless authentication as operating systems and device types would no longer determine the login experience nor unfairly impact productivity. The “most hyped” passwordless solutions by Gartner still require a smartphone or other secondary device and multiple steps on behalf of the user to verify identity. The ideal passwordless authentication solution would solve the problem by removing secondary device requirements, numerous steps, and all possible friction from login for all users and all devices.
Without cross-platform authentication, supporting an organization’s remote workers with secured access to cloud resources becomes impossible. Remote workers depend on cloud applications designed for access, and many remote workers use personal devices to perform business functions, secured or not. To secure access to resources and protect these functions, strong passwordless authentication solutions like Beyond Identity can be a great solution.
Beyond Identity Was Developed For The Modern Workforce
Passwordless solutions should ensure that every device is secured before granting access, obviate the need for passwords to verify identity, and remove usability and cross-platform barriers simultaneously to support the productivity and security of modern workforces.
Beyond Identity was developed to operate across platforms and devices to deliver identity verification leveraging only the strongest factors. Passwords can’t be used anywhere, not even as a backup. Instead, the Beyond Identity authenticator cryptographically binds users’ identities to their enrolled devices leveraging the TPM of user devices. The result is inimitable, unmovable credentials present on the device.
Our authenticator is different—there are no insecure passwords, one-time codes, secondary device requirements, or annoying push notifications. Administrators and users never need to manage their keys or remember a password and the credentials used to authenticate are stored securely in the hardware of the enrolled device.
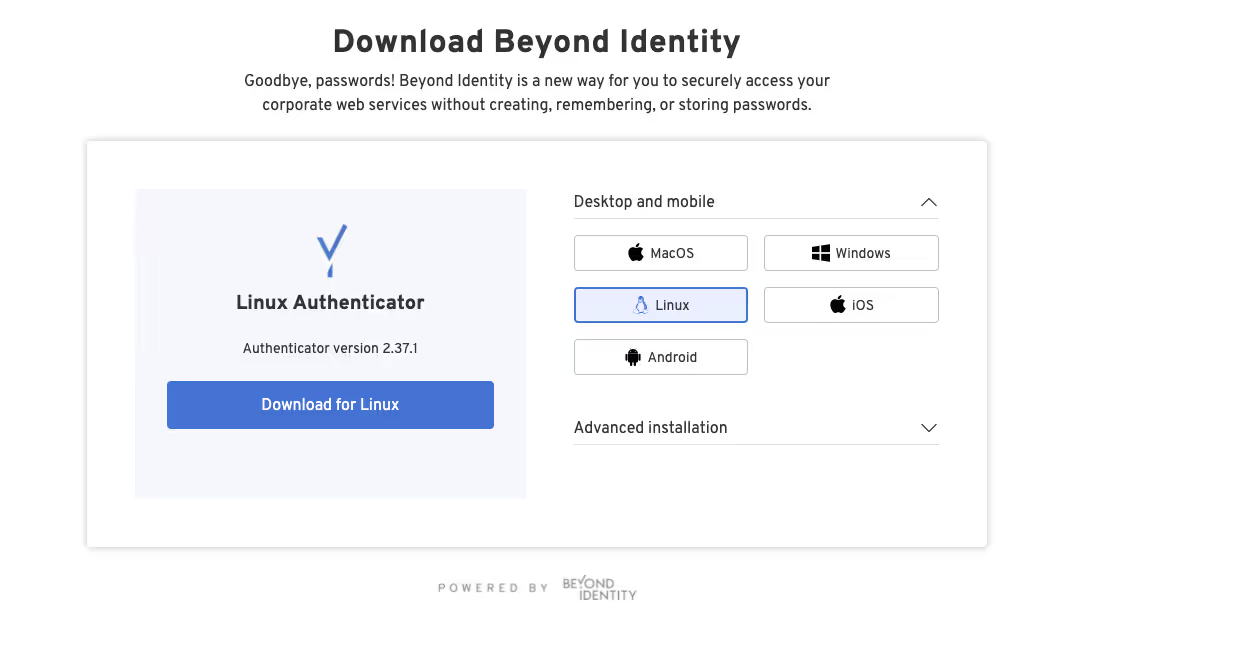
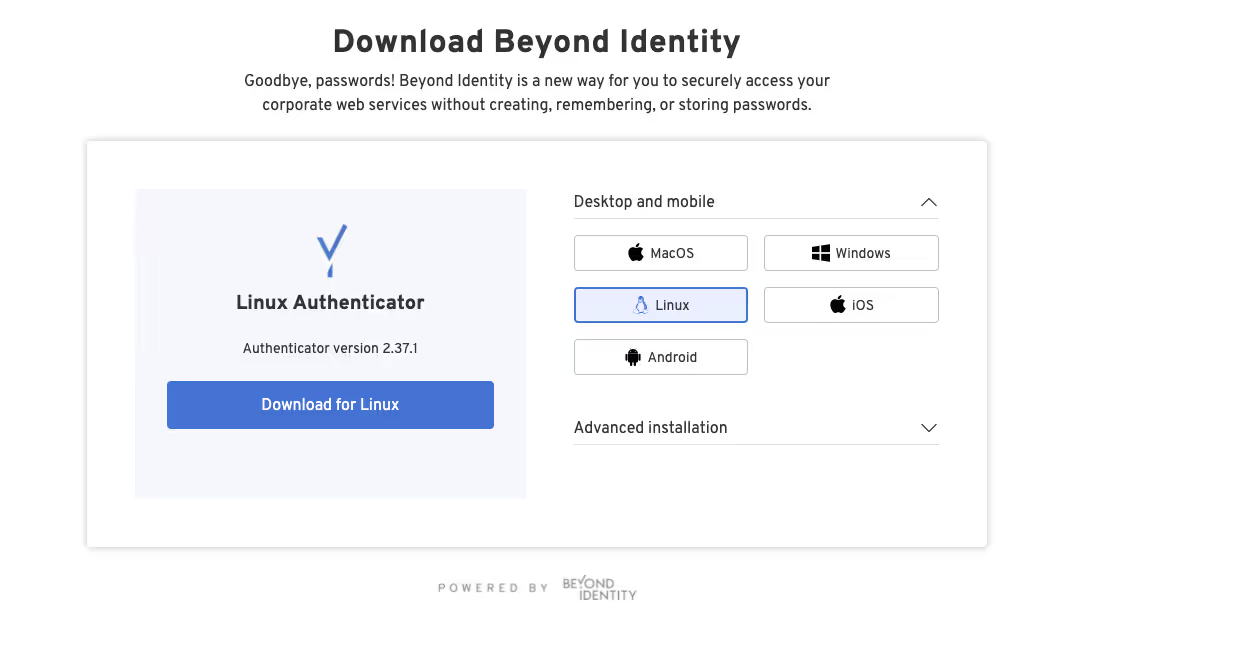
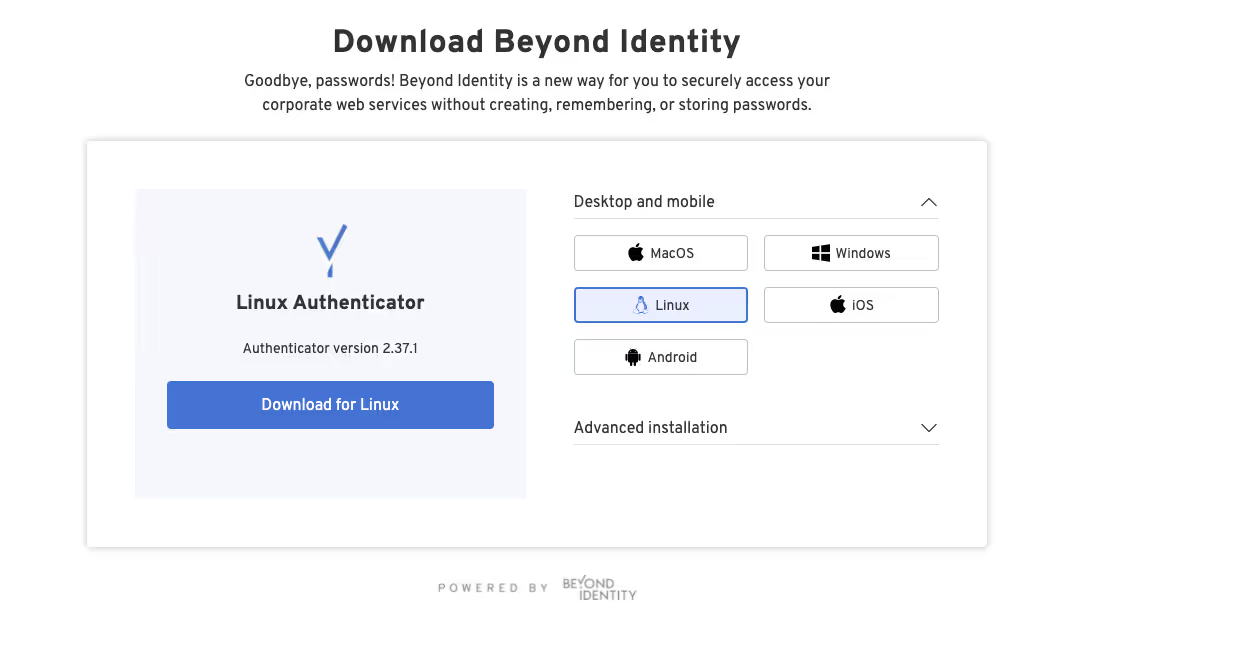
Here are the operating systems we support:

We provide seamless and secure passwordless authentication across Apple, Windows, Android, and Linux operating systems and the devices that run them to support your entire workforce uniformly. Our placement on the TPM also allows us to capture real-time endpoint data like operating system version, security software state, and installed software to inform dynamic access decisions.
To improve the adoption of passwordless authentication methods, security and identity management professionals need a modernized, secure passwordless authentication solution that can guarantee a universally frictionless experience for users regardless of the requestor’s device platform.
See for yourself how Beyond Identity can help you securely authenticate and ensure secured access to cloud resources for your entire workforce.
Passwordless authentication solutions aim to effectively shrink the available attack surface of organizations by removing passwords from the authentication workflow. However, not all passwordless solutions have the same capabilities or features; some of these missing capabilities have created barriers, stagnating passwordless adoption.
In general, widespread adoption of passwordless authentication is hindered by concerns related to usability and cross-platform functionality, with the biggest being the ability to use a particular passwordless authentication method on all device operating systems interacting with organizational resources, most specifically, the ability to remove password prompts in every authentication workflow.
Organizations focused on securing workforce access to critical resources will find this blog post most valuable as we will review these chief concerns surrounding passwordless authentication adoption and cross-platform operability.
Most Passwordless Solutions Were Not Developed To Operate Across Device Platforms
Passwordless authentication, in practice, removes passwords as an authentication factor, though not all “passwordless” authentication eradicates passwords from the authentication workflow as Beyond Identity does. Most “passwordless”, while much more secure than using a password, poses several barriers to adoption. One of those is cross-platform functionality. For example, with Windows Hello For Business, there are no uniform, simple, and seamless solutions to support passwordless access from non-Microsoft devices. People who use an Apple tablet for architectural designs, an Android phone to access Salesforce, or a laptop running a Linux OS for development would still need to use passwords to authenticate and gain access to resources.
The problem many passwordless providers sought to solve was the user experience. If passwordless providers cannot solve passwordless authentication for all use cases, then they’re left with keeping the password as a backup or alternative authentication method for some situations or devices. Passwordless solutions that do not completely eliminate the password from the authentication flow, in all situations, were not built with security requirements of a modern workforce in mind, unlike Beyond Identity.
Why Does Cross-Platform Support Matter for Passwordless?
The requirements of a modern workforce not only demand an answer for cross-platform operability for passwordless authentication, but they also require it to improve the security posture of the organization. These cross-platform challenges force security and identity professionals to reconsider what should be defined as a secure solution for passwordless based on the use cases and needs of businesses transitioning to, or firmly invested in, SaaS applications and cloud computing.
Because Removing Passwords is the Point of Passwordless Authentication
Password-based attacks are the vector of choice for cybercriminals targeting corporate organizations, with over 80% of hacking-related incidents involving credentials and passwords. To appropriately protect against the most significant contributor to data exfiltration, and to eliminate passwords entirely as a threat vector, all users must have secure access to resources, regardless of the device type or operating system they use to request access.
Failing to remove passwords for users on all devices fails to meet the base requirement of passwordless authentication—removing passwords as a factor for authentication.
Because Every Device Is A Work Device
The expansion of work from home and rapid adoption of cloud services has erased the traditional network perimeter, replacing it with sometimes thousands of user endpoints, some managed and others personal devices leveraged for work. In addition, cybercriminals target remote workers, credential stuffing attacks are rising, and 47% of surveyed remote professionals are falling for phishing scams that fuel even more password-based attacks. Therefore, strong passwordless authentication must operate on and ensure the security state of managed and unmanaged devices across platforms and device types to adapt to and defend against evolving cyber risks.
Today, every endpoint is an opportunity for data compromise, so personal devices must be made as secure as company-issued laptops to protect critical resources.
Because Improved Usability Improves Adoption and Compliance
Cross-platform support would ensure consistent experiences for passwordless authentication as operating systems and device types would no longer determine the login experience nor unfairly impact productivity. The “most hyped” passwordless solutions by Gartner still require a smartphone or other secondary device and multiple steps on behalf of the user to verify identity. The ideal passwordless authentication solution would solve the problem by removing secondary device requirements, numerous steps, and all possible friction from login for all users and all devices.
Without cross-platform authentication, supporting an organization’s remote workers with secured access to cloud resources becomes impossible. Remote workers depend on cloud applications designed for access, and many remote workers use personal devices to perform business functions, secured or not. To secure access to resources and protect these functions, strong passwordless authentication solutions like Beyond Identity can be a great solution.
Beyond Identity Was Developed For The Modern Workforce
Passwordless solutions should ensure that every device is secured before granting access, obviate the need for passwords to verify identity, and remove usability and cross-platform barriers simultaneously to support the productivity and security of modern workforces.
Beyond Identity was developed to operate across platforms and devices to deliver identity verification leveraging only the strongest factors. Passwords can’t be used anywhere, not even as a backup. Instead, the Beyond Identity authenticator cryptographically binds users’ identities to their enrolled devices leveraging the TPM of user devices. The result is inimitable, unmovable credentials present on the device.
Our authenticator is different—there are no insecure passwords, one-time codes, secondary device requirements, or annoying push notifications. Administrators and users never need to manage their keys or remember a password and the credentials used to authenticate are stored securely in the hardware of the enrolled device.
Here are the operating systems we support:

We provide seamless and secure passwordless authentication across Apple, Windows, Android, and Linux operating systems and the devices that run them to support your entire workforce uniformly. Our placement on the TPM also allows us to capture real-time endpoint data like operating system version, security software state, and installed software to inform dynamic access decisions.
To improve the adoption of passwordless authentication methods, security and identity management professionals need a modernized, secure passwordless authentication solution that can guarantee a universally frictionless experience for users regardless of the requestor’s device platform.
See for yourself how Beyond Identity can help you securely authenticate and ensure secured access to cloud resources for your entire workforce.
Passwordless authentication solutions aim to effectively shrink the available attack surface of organizations by removing passwords from the authentication workflow. However, not all passwordless solutions have the same capabilities or features; some of these missing capabilities have created barriers, stagnating passwordless adoption.
In general, widespread adoption of passwordless authentication is hindered by concerns related to usability and cross-platform functionality, with the biggest being the ability to use a particular passwordless authentication method on all device operating systems interacting with organizational resources, most specifically, the ability to remove password prompts in every authentication workflow.
Organizations focused on securing workforce access to critical resources will find this blog post most valuable as we will review these chief concerns surrounding passwordless authentication adoption and cross-platform operability.
Most Passwordless Solutions Were Not Developed To Operate Across Device Platforms
Passwordless authentication, in practice, removes passwords as an authentication factor, though not all “passwordless” authentication eradicates passwords from the authentication workflow as Beyond Identity does. Most “passwordless”, while much more secure than using a password, poses several barriers to adoption. One of those is cross-platform functionality. For example, with Windows Hello For Business, there are no uniform, simple, and seamless solutions to support passwordless access from non-Microsoft devices. People who use an Apple tablet for architectural designs, an Android phone to access Salesforce, or a laptop running a Linux OS for development would still need to use passwords to authenticate and gain access to resources.
The problem many passwordless providers sought to solve was the user experience. If passwordless providers cannot solve passwordless authentication for all use cases, then they’re left with keeping the password as a backup or alternative authentication method for some situations or devices. Passwordless solutions that do not completely eliminate the password from the authentication flow, in all situations, were not built with security requirements of a modern workforce in mind, unlike Beyond Identity.
Why Does Cross-Platform Support Matter for Passwordless?
The requirements of a modern workforce not only demand an answer for cross-platform operability for passwordless authentication, but they also require it to improve the security posture of the organization. These cross-platform challenges force security and identity professionals to reconsider what should be defined as a secure solution for passwordless based on the use cases and needs of businesses transitioning to, or firmly invested in, SaaS applications and cloud computing.
Because Removing Passwords is the Point of Passwordless Authentication
Password-based attacks are the vector of choice for cybercriminals targeting corporate organizations, with over 80% of hacking-related incidents involving credentials and passwords. To appropriately protect against the most significant contributor to data exfiltration, and to eliminate passwords entirely as a threat vector, all users must have secure access to resources, regardless of the device type or operating system they use to request access.
Failing to remove passwords for users on all devices fails to meet the base requirement of passwordless authentication—removing passwords as a factor for authentication.
Because Every Device Is A Work Device
The expansion of work from home and rapid adoption of cloud services has erased the traditional network perimeter, replacing it with sometimes thousands of user endpoints, some managed and others personal devices leveraged for work. In addition, cybercriminals target remote workers, credential stuffing attacks are rising, and 47% of surveyed remote professionals are falling for phishing scams that fuel even more password-based attacks. Therefore, strong passwordless authentication must operate on and ensure the security state of managed and unmanaged devices across platforms and device types to adapt to and defend against evolving cyber risks.
Today, every endpoint is an opportunity for data compromise, so personal devices must be made as secure as company-issued laptops to protect critical resources.
Because Improved Usability Improves Adoption and Compliance
Cross-platform support would ensure consistent experiences for passwordless authentication as operating systems and device types would no longer determine the login experience nor unfairly impact productivity. The “most hyped” passwordless solutions by Gartner still require a smartphone or other secondary device and multiple steps on behalf of the user to verify identity. The ideal passwordless authentication solution would solve the problem by removing secondary device requirements, numerous steps, and all possible friction from login for all users and all devices.
Without cross-platform authentication, supporting an organization’s remote workers with secured access to cloud resources becomes impossible. Remote workers depend on cloud applications designed for access, and many remote workers use personal devices to perform business functions, secured or not. To secure access to resources and protect these functions, strong passwordless authentication solutions like Beyond Identity can be a great solution.
Beyond Identity Was Developed For The Modern Workforce
Passwordless solutions should ensure that every device is secured before granting access, obviate the need for passwords to verify identity, and remove usability and cross-platform barriers simultaneously to support the productivity and security of modern workforces.
Beyond Identity was developed to operate across platforms and devices to deliver identity verification leveraging only the strongest factors. Passwords can’t be used anywhere, not even as a backup. Instead, the Beyond Identity authenticator cryptographically binds users’ identities to their enrolled devices leveraging the TPM of user devices. The result is inimitable, unmovable credentials present on the device.
Our authenticator is different—there are no insecure passwords, one-time codes, secondary device requirements, or annoying push notifications. Administrators and users never need to manage their keys or remember a password and the credentials used to authenticate are stored securely in the hardware of the enrolled device.
Here are the operating systems we support:

We provide seamless and secure passwordless authentication across Apple, Windows, Android, and Linux operating systems and the devices that run them to support your entire workforce uniformly. Our placement on the TPM also allows us to capture real-time endpoint data like operating system version, security software state, and installed software to inform dynamic access decisions.
To improve the adoption of passwordless authentication methods, security and identity management professionals need a modernized, secure passwordless authentication solution that can guarantee a universally frictionless experience for users regardless of the requestor’s device platform.
See for yourself how Beyond Identity can help you securely authenticate and ensure secured access to cloud resources for your entire workforce.







.png)






.avif)



.avif)






.avif)

