The Beyond Blog
17 Feb 2026
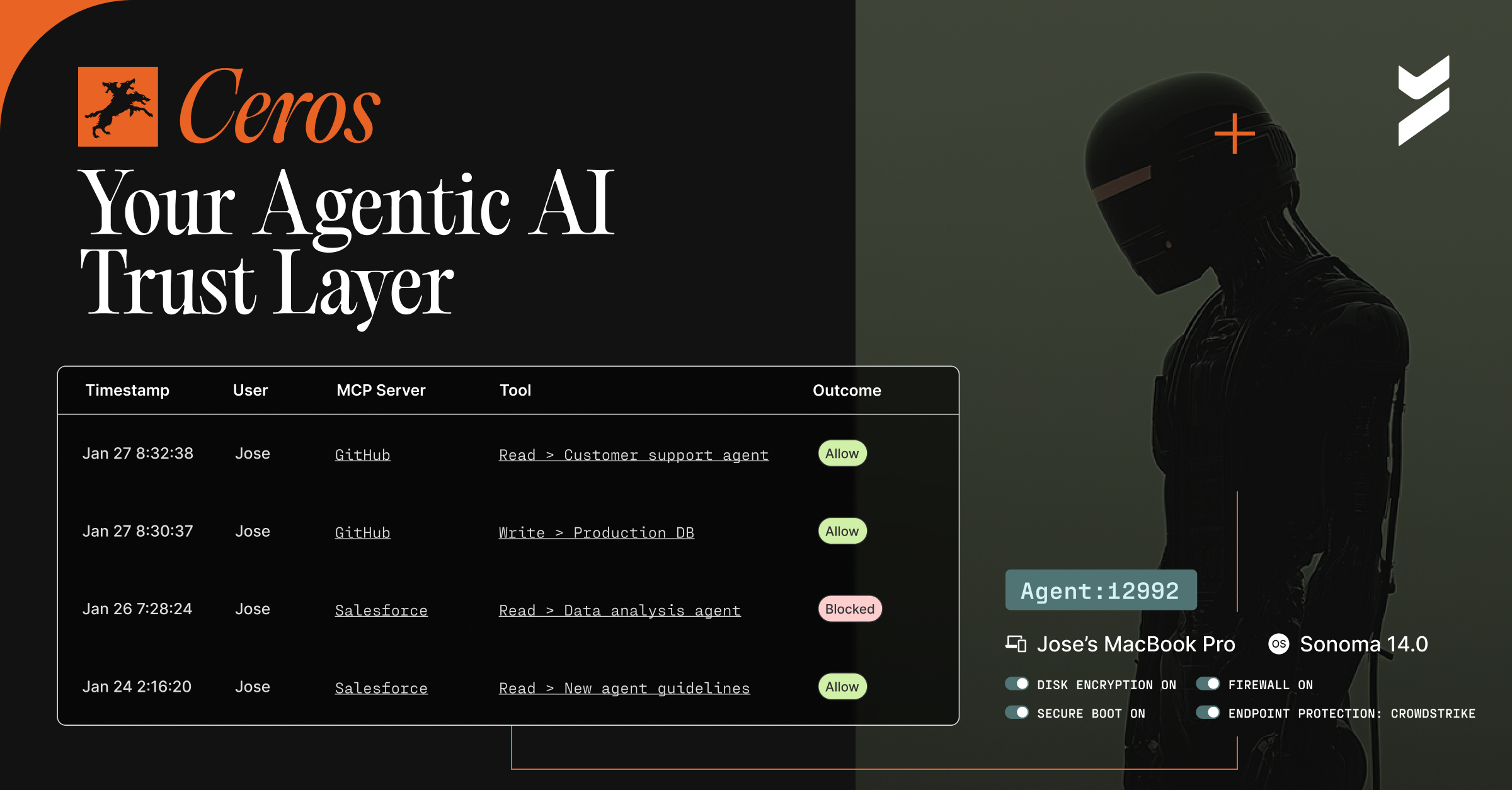
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
%2520(2).avif)
24 Apr 2024
April 24, 2024
Guaranteed Security: From Probabilities to Absolutes
Learn why adopting a new, deterministic approach to cybersecurity is crucial in a new webinar

22 Apr 2024
April 22, 2024
Bridging the Gap: Honoring Veterans in Cybersecurity with VetSec at RSAC
Tom Marsland, Chairman of VetSec, discusses why an upcoming event honoring veterans at RSAC 2024 is so critical for the security industry
.avif)
17 Apr 2024
April 17, 2024
Managing Your Attack Surface with Beyond Identity
Securing your organization's attack surface is essential to protect you from financial losses, reputational damage, operational disruptions, and theft of sensitive information

11 Apr 2024
April 11, 2024
Closing the Gaps in Endpoint Security: Beyond Traditional Solutions
Learn more about advanced endpoint security strategies, modern MFA, zero-trust principles, and unified management for risk management
09 Apr 2024
April 9, 2024
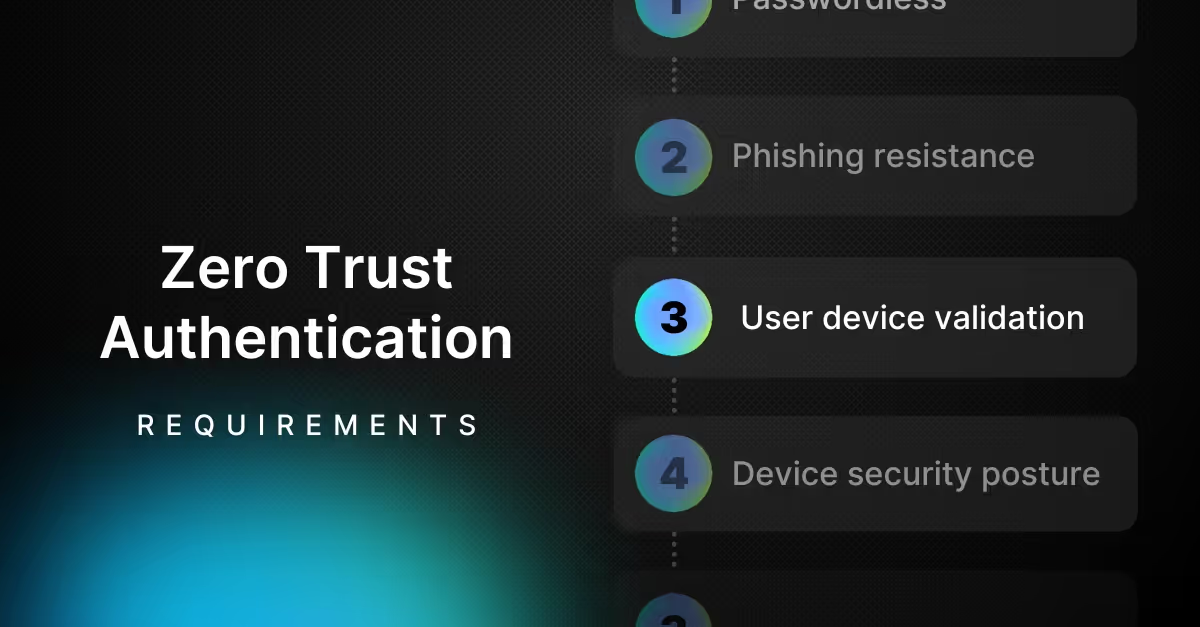
7 Requirements You Must Have in a Zero-Trust Authentication Solution

05 Apr 2024
April 5, 2024
Merging Safely: Beyond Identity's Blueprint for Secure Corporate Expansion
Our platform not only addresses the immediate need for secure authentication but also offers a long-term solution for continuous security improvement. Here's why Beyond Identity stands out in mergers and acquisitions.

01 Apr 2024
April 1, 2024
Hardening Desktop Operating Systems in Security-Conscious Organizations

29 Mar 2024
March 29, 2024
The Power of Zero Trust Authentication
Learn about key uses cases for Zero Trust Authentication in our brief

25 Mar 2024
March 25, 2024
Aligning with NSA's New Cloud Commandments: The Beyond Identity Blueprint for Cloud Security
Learn how organizations can address the NSA's top ten cloud security mitigation strategies

