Eliminate phishing risks
Single-device, passwordless, phishing-resistant MFA to secure every authentication.
Eliminate breaches at the source
Remove your #1 threat vector: the credential.
Secure your entire fleet
Protect access from managed and unmanaged devices, like BYOD, mobile phones, and contractors.
Compliant by default
Meet the toughest mandates from day one; NIST 800-63B, AAL3, and CISA Phishing-Resistant MFA mandates.
Increase user productivity
Remove the top cause of support tickets: passwords. Users stay productive and your team breathes easier.

Built to protect every user,
on every device
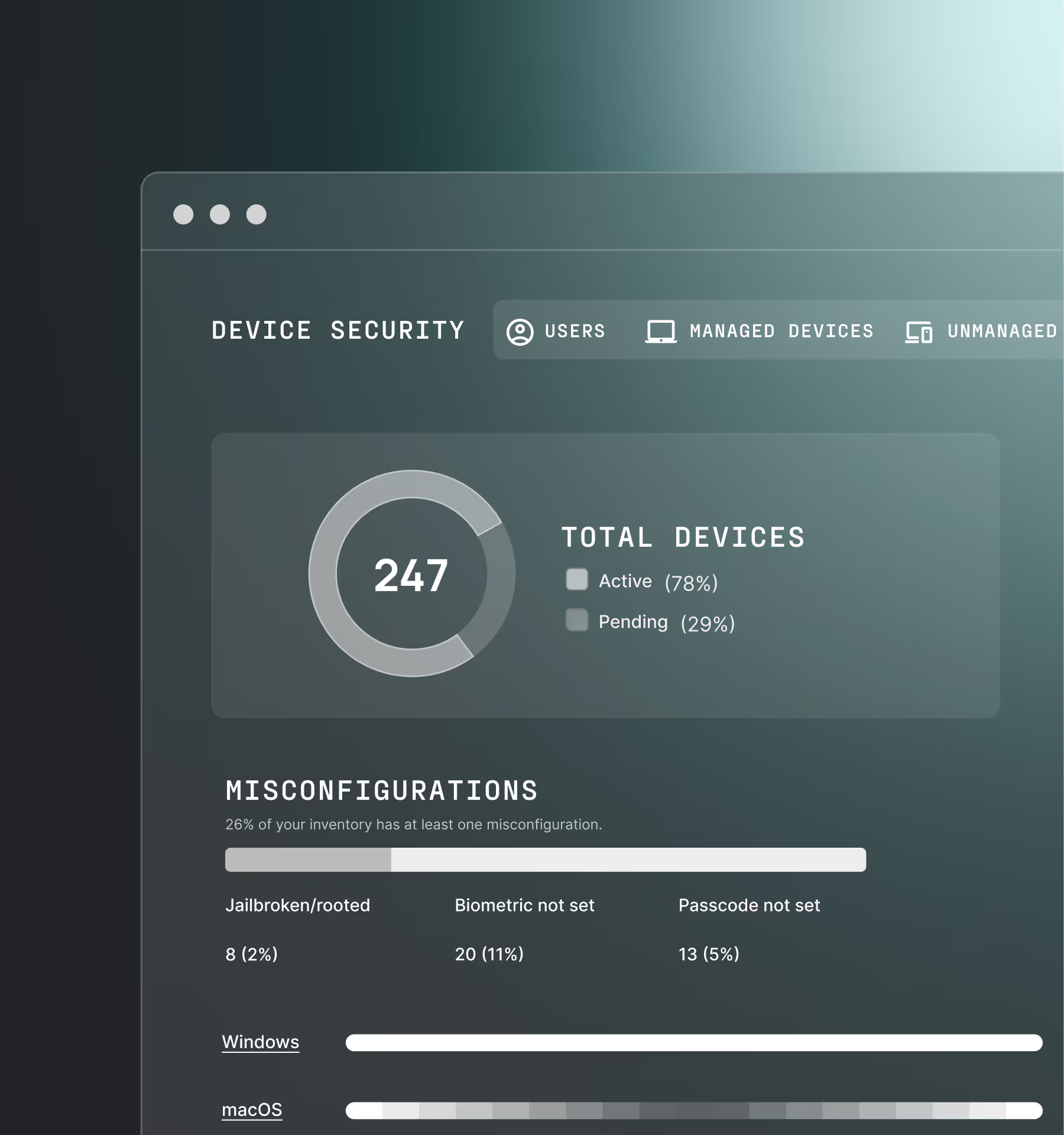
Legacy technology poses a direct threat to your organization by granting access to devices that are out of compliance or whose security posture has changed.
Continuous risk-based authentication
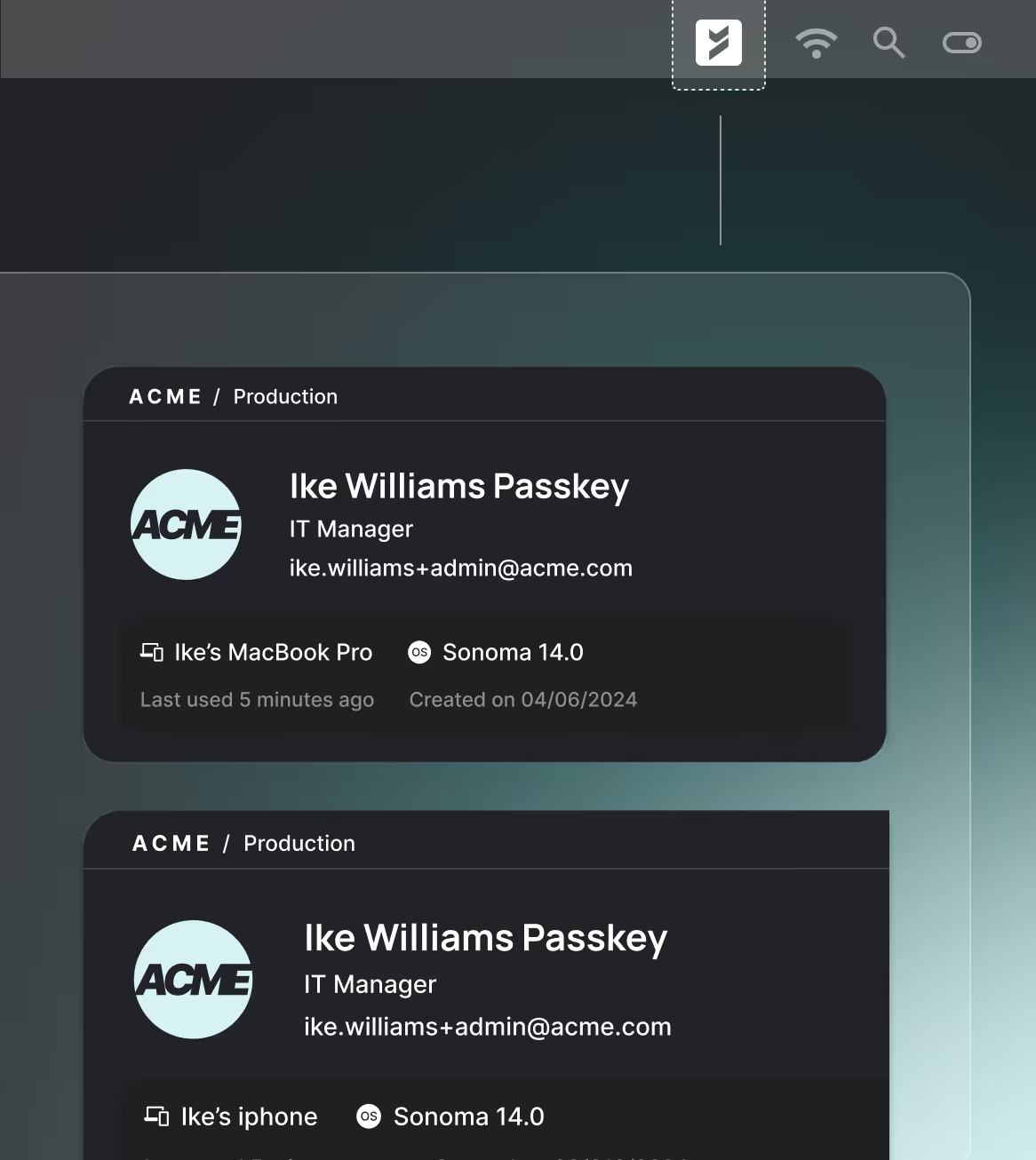
Single-device, passwordless login experiences that takes out the speedbumps in authentication across every device and OS (including Linux!)
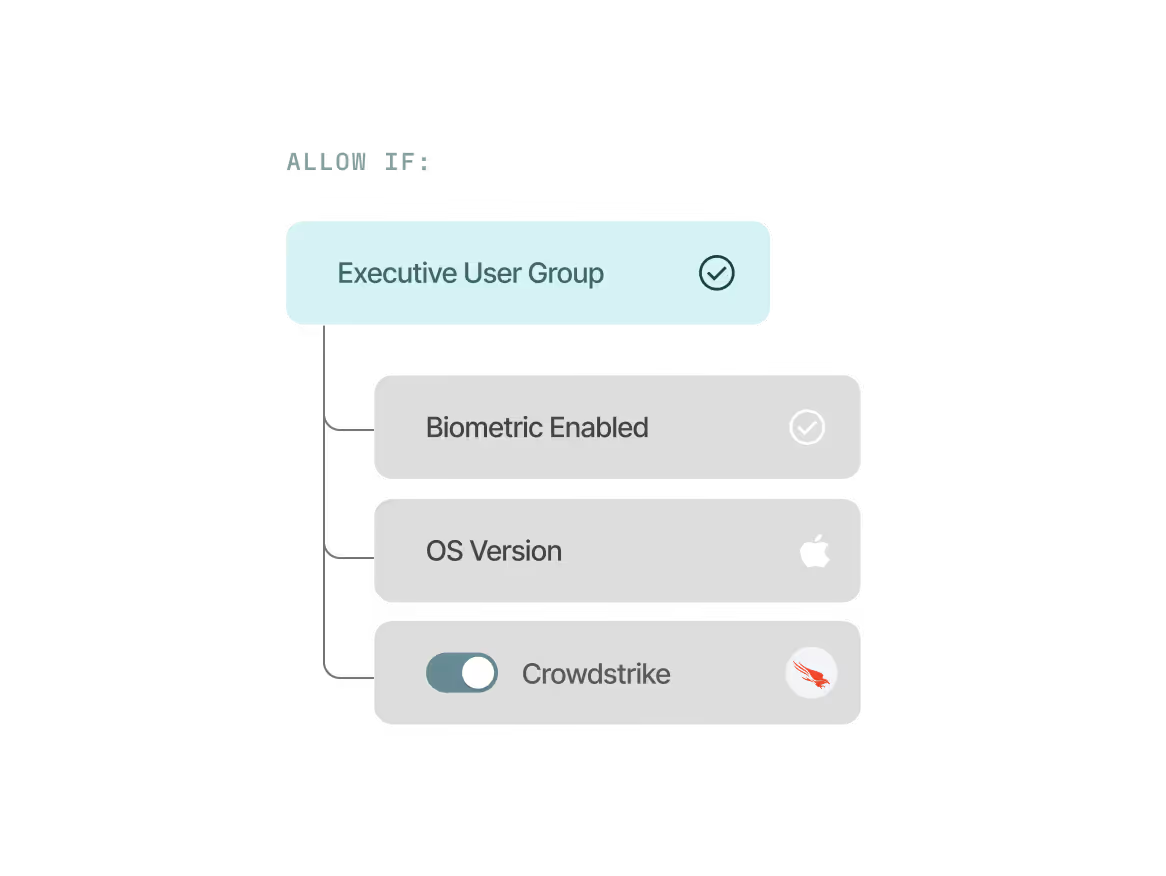
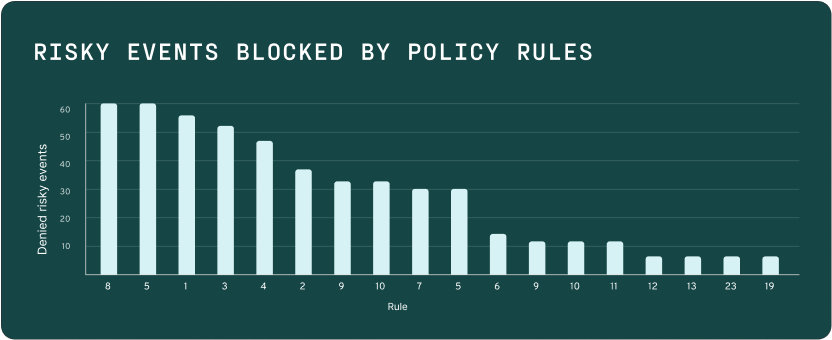
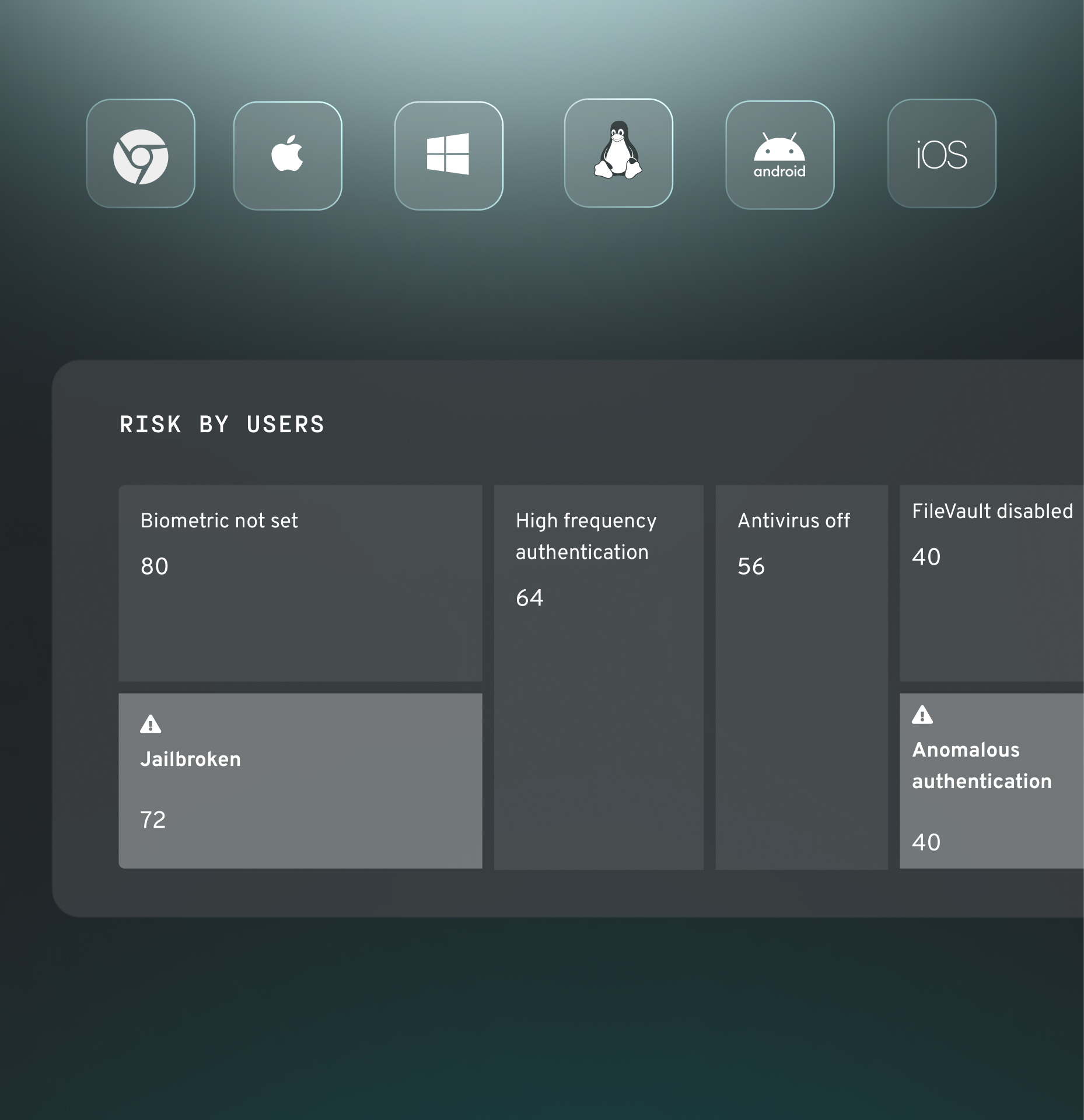
Enforce precise access controls
Easily configure customizable, adaptive risk-based policies tailored to your exact security and compliance requirements. Leverage signals natively collected by Beyond Identity and other security tools in your stack.
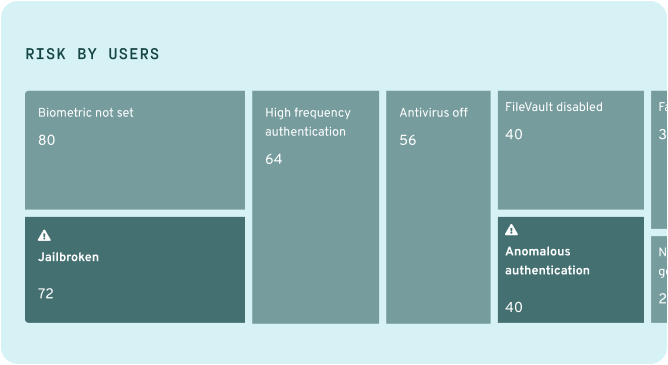
Device security compliance
Ensure access is only granted to a trusted device, managed or unmanaged, with the appropriate security posture as defined by your policy.
Why Beyond Identity?
Traditional MFA providers leaves organizations exposed to modern threats. Beyond Identity’s phishing-resistant MFA solution prevents those threats at the source.
Validating both users and devices continuously, as separate
but equally important requirements for risk-based authentication.
Single-point in time authorization of users only, oftentimes using phishable factors that can leave organizations open to risk.
Frictionless
Frictionless, single-step biometric login on the user's own device. No passwords, codes, or second devices.
Frustrating
High friction with passwords, OTPs, push notifications, and secondary devices that cause drop-off.
100% Phish-resistant
Uses device-bound, universal passkeys that cannot be stolen, shared, or replayed.
Vulnerable
Passwords, SMS codes, and push approvals can all be phished or socially engineered.
operation
100% Passwordless
Fully passwordless on any device and browser. No password in the user experience or stored in your database.
Relies on passwords
Password-dependent. Passwords remain a core attack vector and source of support burden.
Universal
Works on any browser, device, or app, even those that don't support FIDO2 WebAuthn.
Limited
Inconsistent experiences across platforms; some users left behind.
Low lift
Cloud-native, API-first platform with out-of-the-box CIAM integrations, easy-to-use SDKs, and hosted options.
High maintenance
Complex to build, manage, and scale across multiple authentication methods.
Adversaries Exploit Japanese Brokerage Accounts in $700M Stock Manipulation Spree
What Is Push Bombing? And How Beyond Identity Makes It Impossible
Scattered Spider: How to Effectively Defend Against This Aggressive Threat


%20(2).avif)

.avif)
