The Beyond Blog
17 Feb 2026
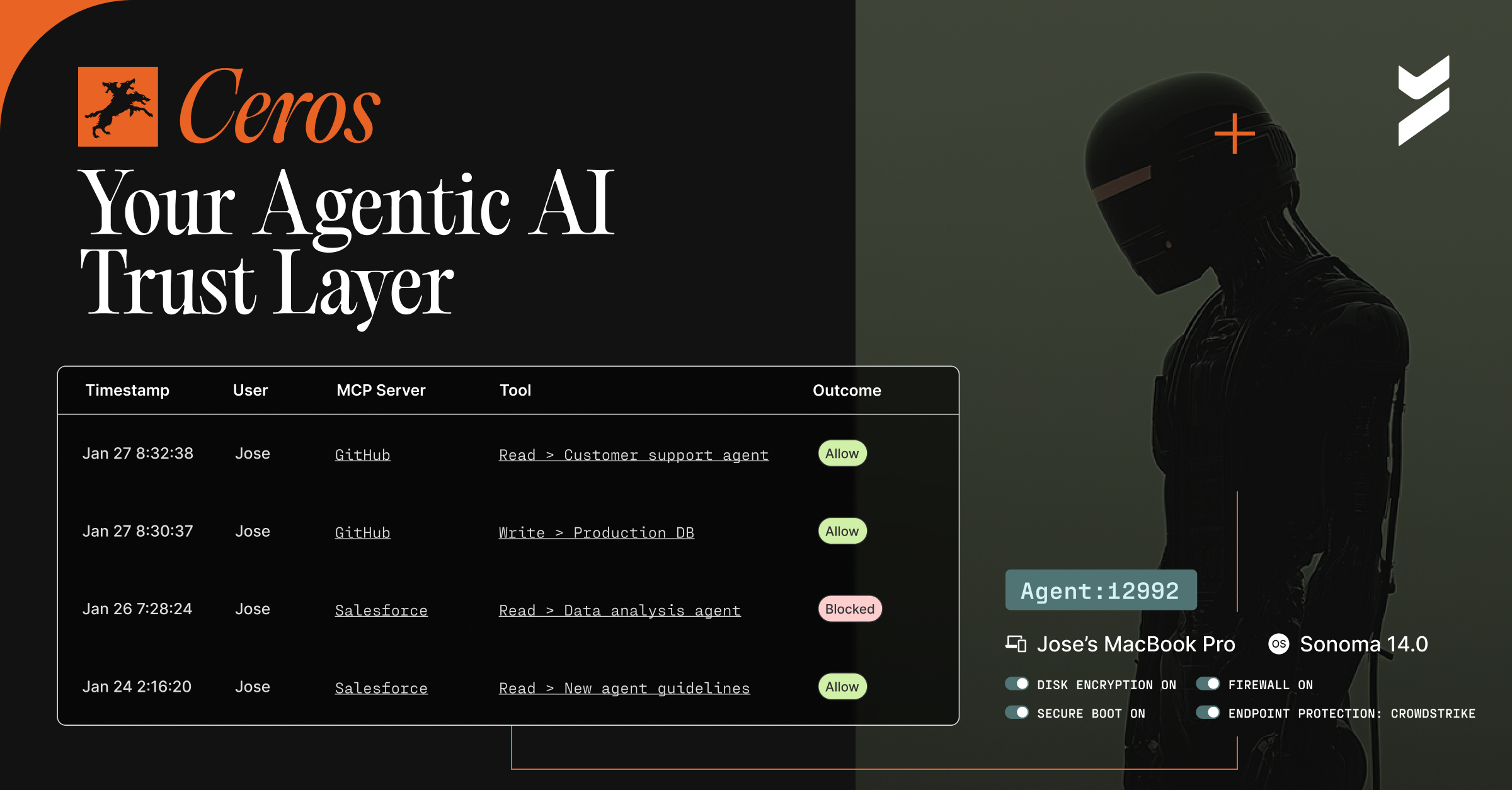
Introducing Ceros: The Agentic AI Trust Layer, Now Open for Public Preview
Secure your AI agents with Ceros, the trust layer that prevents credential theft, enforces policy in real time, and delivers full session visibility. Open for public preview now.
06 Aug 2024
August 6, 2024
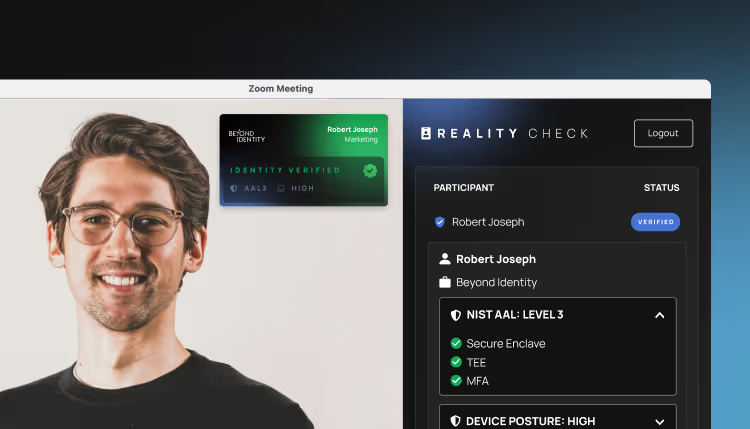
Introducing RealityCheck
RealityCheck uses deterministic signals to prevent deepfake and AI impersonation attacks on high-risk conference calls.

19 Jun 2024
June 19, 2024
NYDFS and Multi-Factor Authentication: What You Need to Know
The NYDFS has demonstrated a focus on the use of strong MFA with its issued fines. Learn what companies need to do to be covered.
17 Jun 2024
June 17, 2024
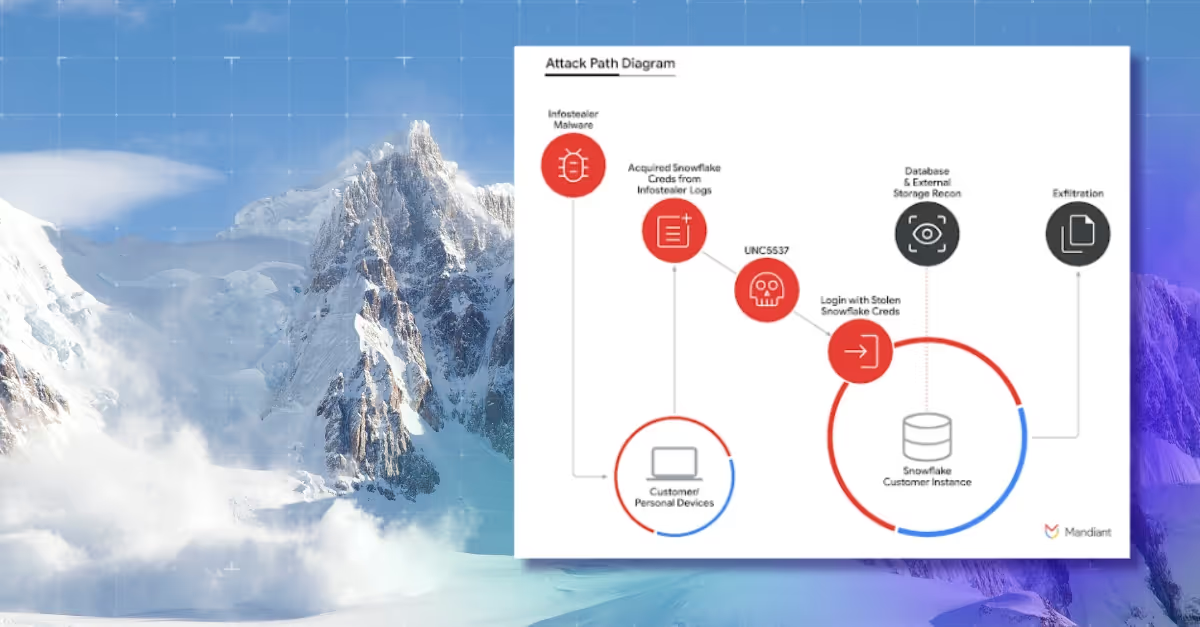
An Avalanche of News About Snowflake Security
Learn the facts about what happened in the recent attack on Snowflake and how Beyond Identity secured Snowflake's enterprise systems.
11 Jun 2024
June 11, 2024
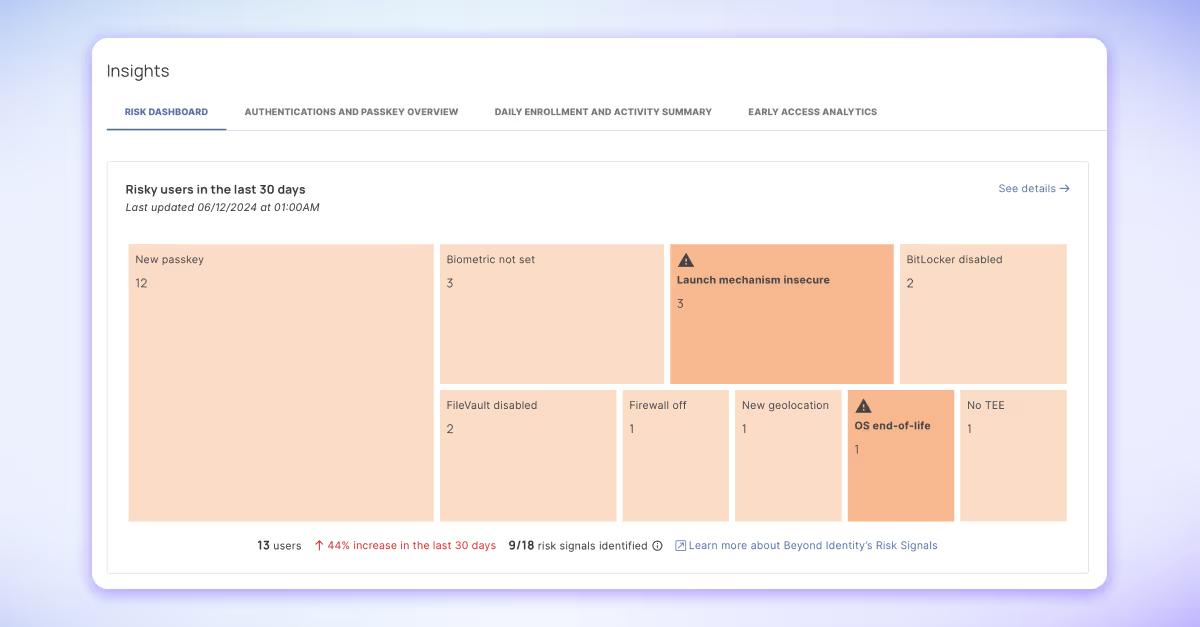
New Feature Announcement: Risk Dashboards
Announcing new Secure Workforce feature, Risk Dashboards, available to all Beyond Identity customers today

03 Jun 2024
June 3, 2024
Statement on Recent Snowflake Security Incident
Snowflake reported a potential compromise of certain customer accounts on May 31st. Here are six actionable recommendations.
22 May 2024
May 22, 2024
No More Compromise: The First and Only Secure-by-Design Access Platform is Here
Legacy SSOs, such as Okta and Microsoft Entra ID, were built for productivity, but failed to secure organizations . Introducing Secure Access, the first unified identity access management platform designed to secure the most vulnerable part of your environment against current and future threats, while being simple to administer and easy to use.

16 May 2024
May 16, 2024
Combating Deepfakes and Generative AI: A Zero Trust Approach to Authenticity Assurance
Generative AI poses significant threats to organizations as they combat deepfake impersonations and increasing phishing attempts. What does a zero trust approach look like for defending against generative AI?

16 May 2024
May 16, 2024
Beyond Identity Signs CISA Secure by Design Pledge
Beyond Identity signs the CISA Secure by Design pledge. Learn more about the pledge and our unwavering commitment to Secure by Design.
30 Apr 2024
April 30, 2024
8 ‘Don’t Miss’ Sessions at RSAC 2024
Learn which sessions we think are a "must see" at RSA Conference 2024

